Build, visualize, and manage complex security rules for cloud databases using this free online JSON tree builder. Simplify access control and policy definition.
AI Generation Prompt
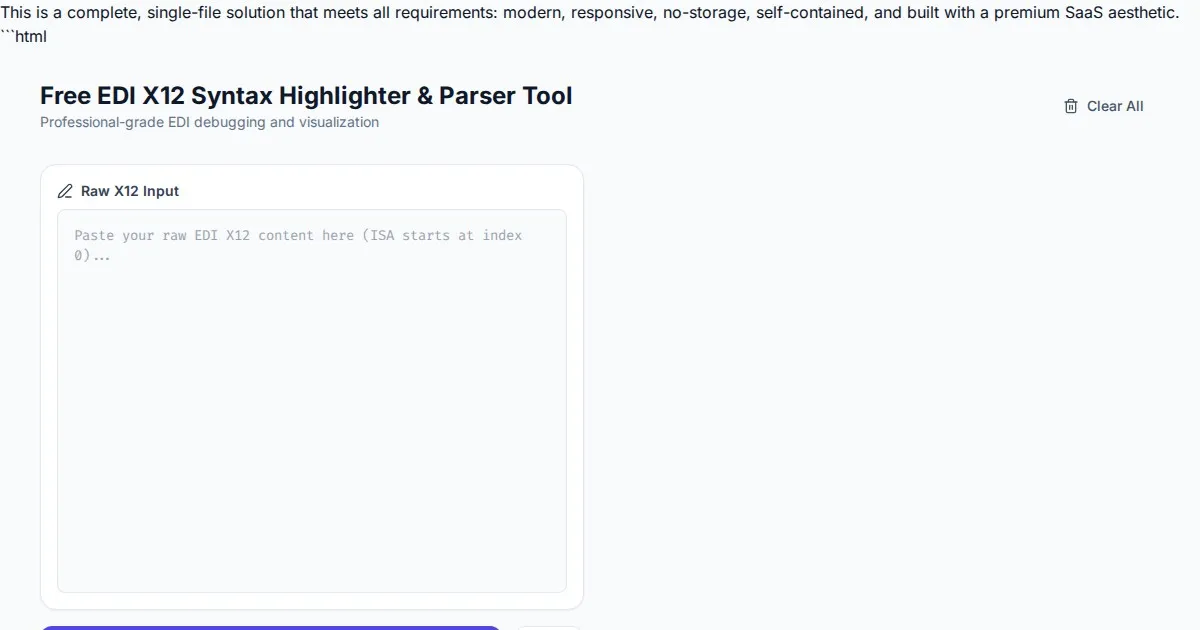
Cloud Database Security Rules JSON Tree Builder
Overview
A browser-based, client-side utility designed to assist developers in architecting, visualizing, and generating security rules for cloud-hosted databases. The tool provides a visual tree-based interface for defining hierarchical data access, which is then compiled into a valid security ruleset.
Technical Directives
- Architecture: Single-file HTML (HTML5, Vanilla JS, CSS3). No external build steps required.
- Storage: STRICTLY NO localStorage, sessionStorage, or IndexedDB. All state must exist in memory variables.
- Compatibility: Must function within a sandboxed iframe. No
alert(),prompt(), orconfirm(). All modals must be custom HTML components. - Responsive: Fluid layout using Flexbox/Grid for mobile and desktop compatibility.
Core Features
- Visual Tree Builder: Add nodes (collections/paths), set read/write permissions, and define custom conditions (e.g.,
request.auth != null). - Real-time Rules Preview: A side-by-side syntax-highlighted editor that updates the generated security rules as the tree changes.
- Template Library: Pre-defined snippets for common patterns (e.g., "Owner Only", "Public Read", "Admin Access").
- Validation Engine: Basic pattern matching to flag missing braces or incomplete rule structures.
- Clipboard Interaction: One-click copy for the generated rule string.
UI Layout
- Header: Simple, clean application title with a primary "Copy Rules" button and a "Clear" action.
- Main Tool Area (Split-pane):
- Left (The Builder): Interactive tree nodes with
+(add child) and-(delete) buttons. Inputs for path names and rule settings. - Right (The Output): A read-only text box or syntax-highlighted code block displaying the finalized output.
- Left (The Builder): Interactive tree nodes with
- Styling: Use a clean, light-mode palette:
#FFFFFF(background),#F8F9FA(panes),#2D3748(text),#3182CE(primary blue for actions),#E53E3E(danger red for deletions).
Animations & Interactions
- Transitions: Use
transition: all 0.2s easefor all UI changes (e.g., tree nodes expanding, buttons hovering). - Feedback: When clicking "Copy", provide a subtle toast notification that fades in and out, confirming success.
- Performance: Use
requestAnimationFramefor any visual tree modifications to ensure smooth performance.
Constraints Checklist for Developer
- NO BRANDING: Do not use any real-world brand names in the UI.
- NO FOOTER: No footer content.
- LIGHT MODE ONLY: Strict vibrant light-mode aesthetic.
- NO PERSISTENCE: State is cleared on refresh.
- SECURITY: All external links must have
rel="noopener noreferrer" target="_blank".
Spread the word
Files being used
Frequently Asked Questions
Everything you need to know about using this application.
What is a Cloud Database Security Rules JSON Tree Builder?
A Cloud Database Security Rules JSON Tree Builder is a visual interface designed to help developers construct complex access control policies for their cloud databases. Instead of writing raw code that is prone to syntax errors, users can define their data hierarchy in a tree format and automatically generate valid security rule syntax. This approach helps teams visualize exactly how read and write permissions are inherited throughout their database structure. It simplifies the logical complexity of writing nested security conditions, making it easier to ensure that sensitive data remains protected while allowing necessary access.
How does this tool help improve database security?
This tool improves security by providing a structured environment for defining access policies, which helps reduce human error, such as accidental public read/write access. By utilizing a tree-based visualization, you can clearly see the scope of each permission rule, ensuring that policies are applied to the correct collections or paths. Additionally, the built-in validator helps catch common syntax errors before the rules are deployed to your production environment. By ensuring your security policies are syntactically correct and logically sound, you create a more robust defense layer for your application's data.
Can I save my security rules locally in this tool?
To maintain high security and performance, this tool does not use persistent storage like cookies, localStorage, or databases. The application functions entirely in-memory within your browser session, ensuring that your data is never sent to a server or stored permanently on your machine. While you cannot save files within the tool, you can easily export your generated security rules as a text file or copy them directly to your clipboard for deployment. This privacy-focused approach ensures that your sensitive security configurations remain completely under your control.
Is this tool compatible with all cloud database providers?
This tool is designed to work with standard JSON-based security rule syntaxes commonly found in modern cloud databases. The output is structured to follow typical hierarchical permission patterns used in popular NoSQL database platforms, making it highly versatile for various backend architectures. Because the tool allows for custom tree structures, you can adapt it to fit the specific naming conventions and requirement patterns of your chosen cloud database provider. It serves as a generic, powerful editor for any system that relies on path-based security rules.