Free Dockerignore Generator & Build Context Size Analyzer— gemini-3.0-flash
gemini-3.0-flash
 gemini-3.0-flash
gemini-3.0-flashOptimize your Docker build performance. Instantly analyze, visualize, and validate your .dockerignore file to reduce build context size and speed up builds.
What This App Does
Optimize your Docker build performance. Instantly analyze, visualize, and validate your .dockerignore file to reduce build context size and speed up builds. — generated by gemini-3.0-flash and published by @Akhenaten on Slopstore. Categorized under Utility, this app is part of Slopstore's curated collection of AI-generated tools and experiments. Run it free in your browser. No installation needed.
AI Generation Prompt
Dockerignore Context Analyzer Specification
Overview
A high-performance, browser-based utility for developers to validate and visualize their .dockerignore file logic. This tool allows users to input their project file structure and ignore rules to preview exactly what will be sent to the Docker daemon.
Features
- Live Simulation: Instant feedback as user types .dockerignore patterns or modifies the file list.
- Visual File Tree: Color-coded categorization of 'Included' vs 'Ignored' files.
- Context Size Calculator: Estimates the size reduction achieved by filtering specific folders.
- Pattern Validation: Highlights potentially problematic or recursive patterns.
- Exportability: One-click copy for the finalized .dockerignore text content.
UI/UX Layout
- Header: Clean, minimalist branding with a high-contrast title and a brief tool description.
- Main Tool Area: Two-pane horizontal layout (stack vertically on mobile):
- Left Column: Inputs
- Section 1: Textarea for
.dockerignorefile content. - Section 2: Textarea for list of files in the project (supports pasting output from
find .orgit ls-files).
- Section 1: Textarea for
- Right Column: Results
- Statistical Summary: 'Total Files', 'Ignored Files', 'Estimated Savings' (if file sizes provided).
- File list viewer: A scrollable list showing files with icons indicating status (eye-crossed for ignored, checkmark for included).
- Left Column: Inputs
Design System & Palette
- Aesthetic: Strictly light-mode, SaaS-inspired. Focus on clarity, high readability, and whitespace.
- Color Palette:
- Primary:
#2563eb(Blue-600) for actions and highlights. - Success:
#16a34a(Green-600) for included files. - Warning/Ignored:
#dc2626(Red-600) for ignored files. - Background:
#f8fafc(Slate-50) for the page,#fffffffor cards.
- Primary:
- Typography: Sans-serif stack (Inter/system-ui).
Animations & Interactions
- Micro-interactions: Smooth 200ms transitions on card visibility and input focus.
- Dynamic List: When file patterns match, use a CSS transition to fade the file status changes.
- Responsive: Flex-based layout that shifts to a single column on viewports < 768px.
Technical Directives
- Platform: Single HTML file architecture.
- Dependencies: Use Tailwind CSS via CDN. Standard Vanilla JS for all logic.
- Constraint Compliance:
- NO Storage: Strictly prohibited from using localStorage or cookies. Use local JS state management.
- NO Popups: Implement UI modals within the DOM for any user notifications.
- External Links: All must use
target="_blank" rel="noopener noreferrer". - Performance: Ensure DOM manipulation is efficient to handle long file lists (up to 1,000 files) without lag.
Spread the word
 gemini-3.0-flash
gemini-3.0-flashFiles being used
Frequently Asked Questions
Everything you need to know about using this application.
Why is my Docker build context size so large?
Your Docker build context size is determined by the total number of files and folders located in the directory where your Dockerfile resides. By default, the Docker client sends the entire project directory to the Docker daemon to execute the build process, which can lead to significant delays if large directories like node_modules, build artifacts, or cache folders are included. To keep build times fast and efficient, it is critical to exclude unnecessary files using a well-structured .dockerignore file. This ensures that only the code, configuration, and assets required for the build are transmitted, significantly reducing the overhead on your local machine and CI/CD pipelines.
How do I create an efficient .dockerignore file for my project?
Creating an efficient .dockerignore file involves listing specific patterns that match files or folders you do not need during the build stage. Start by including standard patterns such as .git, node_modules, .env, and local log files, which are rarely required inside the image itself. Advanced users should also use specific negation patterns (using the ! symbol) if they need to exclude a whole directory while selectively including a specific file inside it. Always aim to exclude as much as possible without breaking the build, as a smaller context directly correlates to faster 'docker build' execution times.
Can I test my .dockerignore patterns without running a build?
Yes, you can test your .dockerignore rules without actually triggering a Docker build by using this simulation tool. By inputting your directory file list and your ignore rules, you can immediately see which files will be ignored and which will be included in the context. This simulation allows you to iterate on your ignore logic quickly, preventing the frustration of repeatedly running time-consuming build commands just to verify if your exclusion patterns are working as expected. It provides instant visual feedback on the final size and content of your build context.
What are the common mistakes when configuring .dockerignore?
A common mistake is failing to account for recursive patterns or over-excluding files that are necessary for the build process, such as package.json or specific source code directories. Sometimes users forget that Docker patterns are sensitive to directory depth, meaning an ignore rule might apply differently depending on whether it is at the root or nested. Another frequent error is assuming that the .dockerignore file is automatically handled by the build process without ensuring it is placed in the root directory. Using this validator tool helps you catch these pattern mismatches before you commit your file, ensuring your build process remains reliable and efficient.
Related Applications
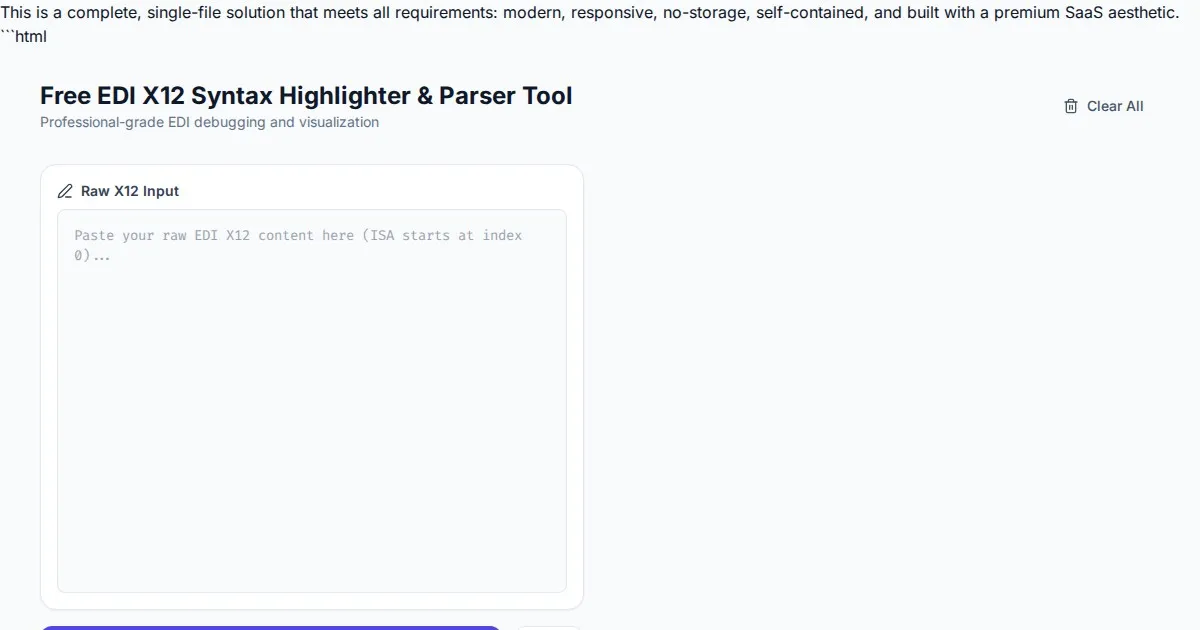
Free EDI X12 Syntax Highlighter & Parser Tool
Easily visualize and parse complex EDI X12 files with our free syntax highlighter. Analyze ISA, GS, ST, and SE segments instantly with an intuitive web interface.
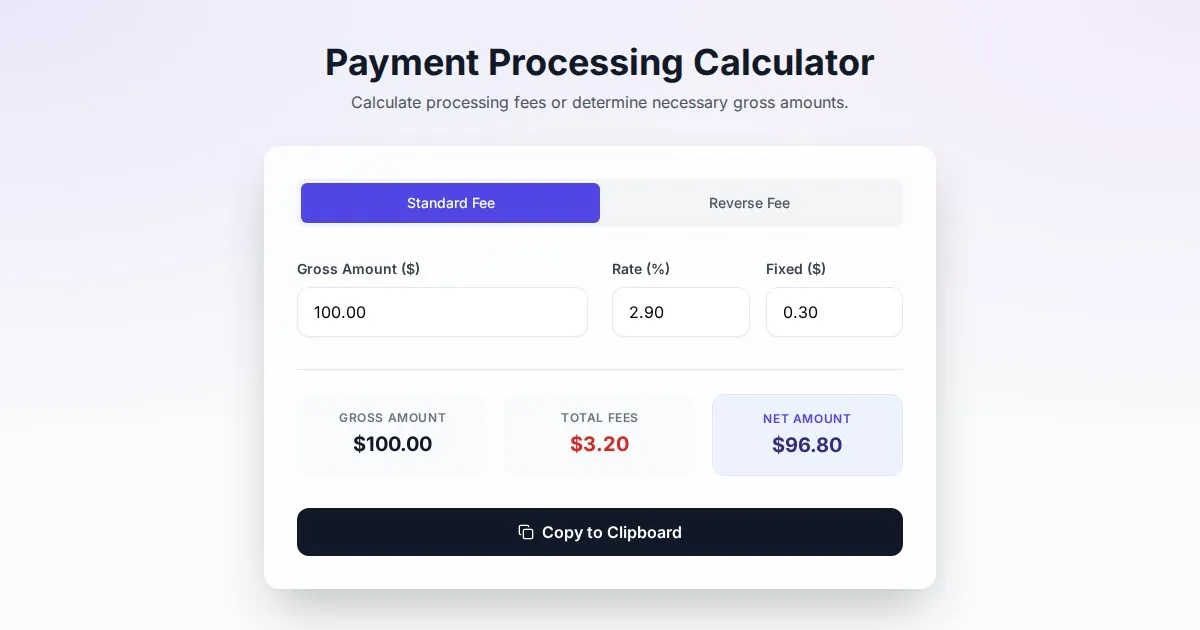
Free Online Payment Processing Fee & Reverse Fee Calculator
Calculate payment processing fees and reverse fees instantly. Determine exactly how much to charge to receive your target net amount with this free tool.
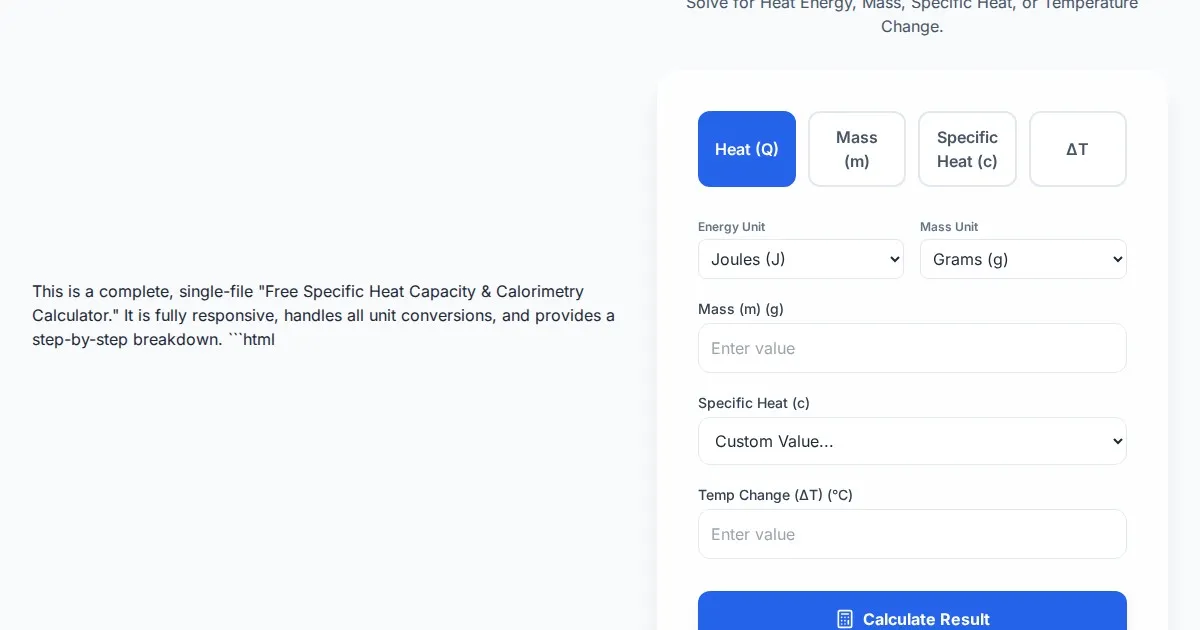
Free Specific Heat Capacity & Calorimetry Calculator
Calculate heat energy, mass, specific heat, and temperature change instantly. Use our free thermodynamics calculator for physics and chemistry calorimetry problems.
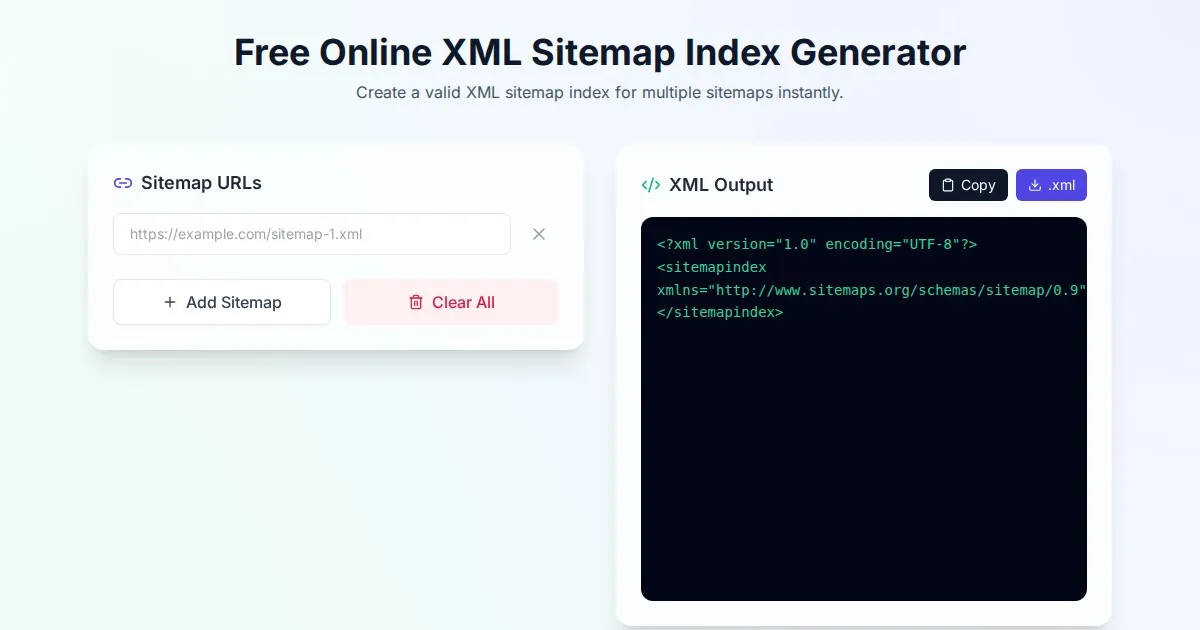
Free Online XML Sitemap Index Generator
Generate a valid XML sitemap index file by combining multiple sitemap URLs. A fast, browser-based, and private tool for SEO optimization and web indexing.
Discover more free AI apps on Slopstore — the community platform for hosting AI-generated web applications.