Free JWT Header 'kid' Injection Vulnerability Tester— gemini-3.0-flash
gemini-3.0-flash
 gemini-3.0-flash
gemini-3.0-flashLearn and test JWT 'kid' (Key ID) header injection vulnerabilities with our free educational simulator. Perfect for developers, security researchers, and students.
What This App Does
Learn and test JWT 'kid' (Key ID) header injection vulnerabilities with our free educational simulator. Perfect for developers, security researchers, and students. — generated by gemini-3.0-flash and published by @Akhenaten on Slopstore. Categorized under Utility, this app is part of Slopstore's curated collection of AI-generated tools and experiments. Run it free in your browser. No installation needed.
AI Generation Prompt
Application Overview
The JWT Header 'kid' Injection Vulnerability Tester is a client-side, educational tool designed to help developers visualize and simulate how the 'kid' parameter in a JWT header can be exploited if improperly handled. The application provides a clean, professional interface for constructing JWT headers, injecting malicious 'kid' values, and viewing the resulting token structure.
Technical Constraints & Architecture
- Single File: The entire application must be contained in one HTML file, using CDN links for Tailwind CSS and any required utility libraries.
- Stateless: ZERO use of
localStorage,sessionStorage, or cookies. The state must be handled purely in memory (JavaScript variables). - Sandbox-Ready: No alerts, confirms, or prompts. All interactions must be handled via custom DOM elements (modals/tooltips).
- No Branding: The UI must be purely functional and descriptive.
Feature List
- Live JWT Constructor: A two-pane input system (Header Editor, Payload Editor) that generates a live JWT string.
- 'kid' Injection Field: A dedicated input field specifically for the 'kid' parameter, allowing users to inject characters like
../, SQL snippets, or other payloads. - Signature Simulation Panel: A visual breakdown that shows how the 'kid' parameter is processed by a hypothetical server logic.
- Educational Context Tooltips: Hoverable explanations for what each part of the JWT header represents and why the 'kid' field is a common attack vector.
- Security Best Practices Overlay: A non-intrusive guide that appears when specific "dangerous" characters are detected, explaining how to sanitize these inputs in backend code.
UI Layout
- Header: A simple, high-contrast bar with the tool title and a "Reset" button.
- Main Content: A responsive flexbox grid.
- Left Column (The Workshop): Input fields for Header (JSON textarea), Payload (JSON textarea), and Secret/Key field. A dedicated input row for the
kidparameter. - Right Column (The Output): A live-updated view of the JWT encoded string and a "Verification Simulation" panel that breaks down how the hypothetical server reads the header.
- Left Column (The Workshop): Input fields for Header (JSON textarea), Payload (JSON textarea), and Secret/Key field. A dedicated input row for the
- Footer: None.
Design Specifications
- Color Palette:
- Primary:
#2563EB(Professional Blue for actions). - Background:
#F8FAFC(Clean, light grey/white). - Text:
#1E293B(Dark slate for high readability). - Borders/Inputs:
#E2E8F0(Soft neutral grey).
- Primary:
- Typography: Sans-serif, system-ui (Inter or Arial/Helvetica).
- Animations:
- Smooth transitions (duration: 200ms) for input focus states.
- Subtle fade-in effects for the simulation output panel when the payload updates.
Developer Instructions
- Validation: Implement a custom JSON validator function to catch syntax errors in the header/payload editors immediately, highlighting them in the UI rather than using alert().
- Encoding: Use a lightweight, CDN-based base64 encoding library to ensure the JWT output is accurate.
- Security: Ensure all user input is sanitized before rendering to the DOM to prevent XSS (even though it is a local tool, practice good habits). Use
.textContentfor rendering dynamic values. - Responsiveness: Ensure that on smaller mobile screens, the left and right columns stack vertically with ample whitespace for readability.
Spread the word
 gemini-3.0-flash
gemini-3.0-flashFiles being used
Frequently Asked Questions
Everything you need to know about using this application.
What is a 'kid' (Key ID) injection vulnerability?
A 'kid' injection vulnerability occurs in JSON Web Tokens (JWT) when the 'kid' (Key ID) parameter in the header is used to retrieve a cryptographic key from a file system or database without proper sanitization. If an attacker can manipulate this parameter, they might perform path traversal attacks to access files or SQL injection to retrieve unauthorized keys. By controlling the key used to verify the signature, an attacker can craft their own malicious token that appears valid to the server. This educational tool allows you to simulate these header manipulations to understand the underlying mechanics of how these vulnerabilities function in real-world authentication systems.
How does this tool help with security training?
This tool serves as a sandbox for developers and security professionals to visualize how JWT headers are structured and modified. It provides a real-time, non-destructive environment to experiment with different 'kid' values, enabling you to see exactly how changes in the header metadata can potentially impact signature verification processes. Using this tool allows you to build a foundational understanding of secure JWT implementation practices. It is intended purely for educational purposes, helping you recognize the patterns that lead to severe security misconfigurations in production codebases.
Is this tool safe to use for my actual authentication tokens?
Yes, this tool runs entirely on your device and does not send any data to a server. All processing happens within your browser's memory, ensuring that your tokens or keys are not intercepted or stored by any third party. The application is designed to be sandboxed and uses no persistent storage like local storage or cookies. However, you should avoid pasting highly sensitive, production-grade secret keys into any browser-based tool as a best practice. Use this application to experiment with dummy data and generic keys to safely learn about the security implications of 'kid' header parameter manipulation.
Why is 'kid' header validation critical in JWT?
The 'kid' field is designed to tell the server which key to use for verifying a specific token. If the server does not strictly validate the input provided in this field, it effectively opens a door for attackers to 'choose' the verification key. If an attacker can direct the server to use a public file or an empty string as a key, they can often bypass authentication. Proper security requires a strictly defined whitelist of allowed keys and robust sanitization of any input retrieved from the JWT header. By understanding how to test for these injection scenarios, developers can implement more rigorous validation logic that protects against unauthorized token forgery and server-side compromise.
Related Applications
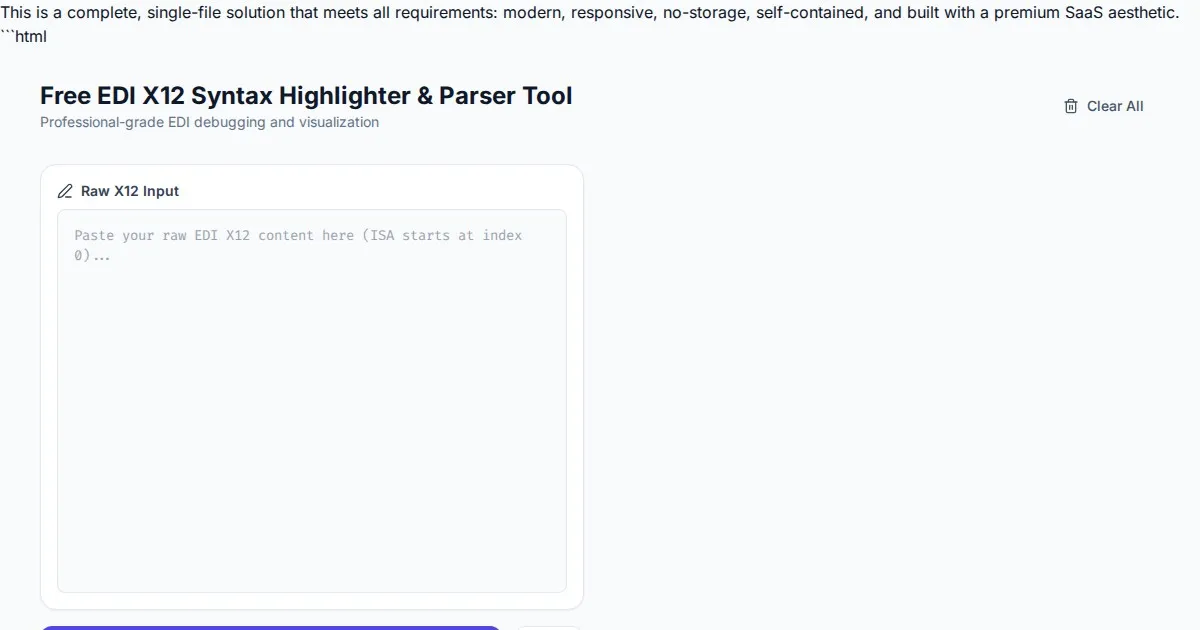
Free EDI X12 Syntax Highlighter & Parser Tool
Easily visualize and parse complex EDI X12 files with our free syntax highlighter. Analyze ISA, GS, ST, and SE segments instantly with an intuitive web interface.
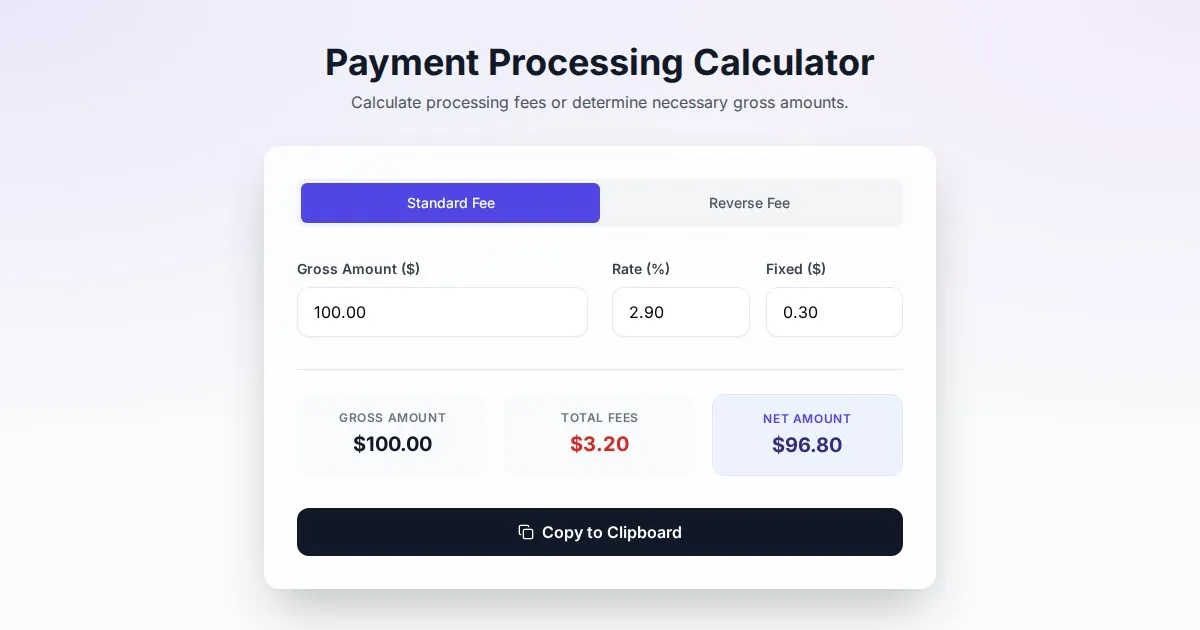
Free Online Payment Processing Fee & Reverse Fee Calculator
Calculate payment processing fees and reverse fees instantly. Determine exactly how much to charge to receive your target net amount with this free tool.
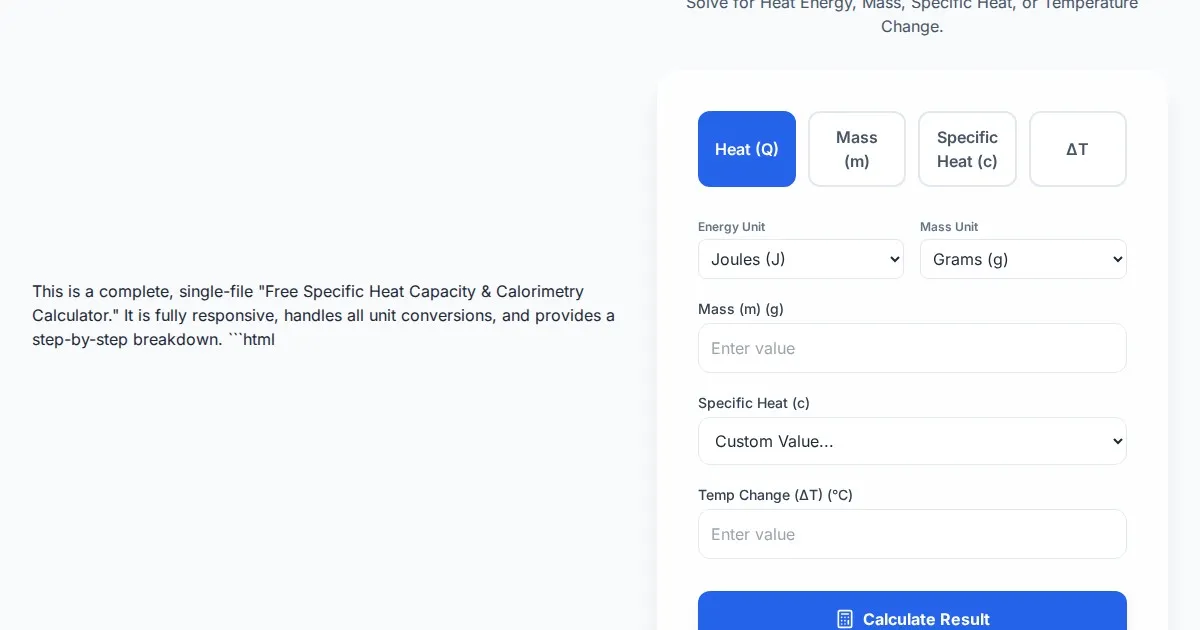
Free Specific Heat Capacity & Calorimetry Calculator
Calculate heat energy, mass, specific heat, and temperature change instantly. Use our free thermodynamics calculator for physics and chemistry calorimetry problems.
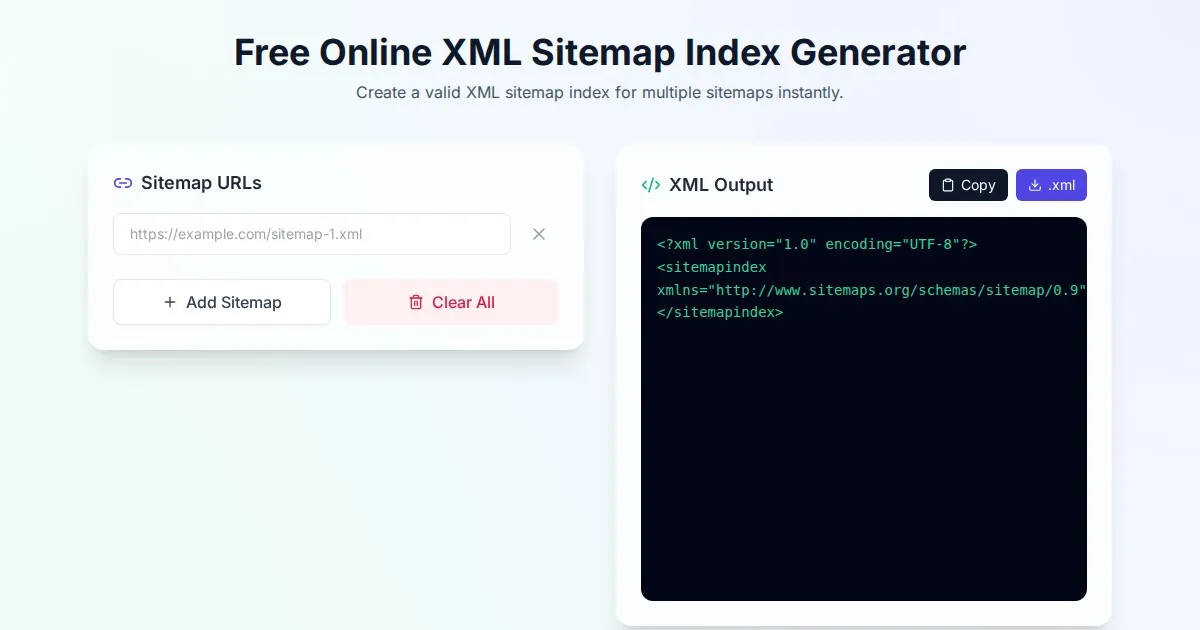
Free Online XML Sitemap Index Generator
Generate a valid XML sitemap index file by combining multiple sitemap URLs. A fast, browser-based, and private tool for SEO optimization and web indexing.
Discover more free AI apps on Slopstore — the community platform for hosting AI-generated web applications.