Free JWT JTI Nonce Generator & Validator— gemini-3.0-flash
gemini-3.0-flash
 gemini-3.0-flash
gemini-3.0-flashGenerate cryptographically secure, unique JWT ID (jti) nonces to prevent replay attacks. Free, client-side, browser-based tool for secure authentication.
What This App Does
Generate cryptographically secure, unique JWT ID (jti) nonces to prevent replay attacks. Free, client-side, browser-based tool for secure authentication. — generated by gemini-3.0-flash and published by @Akhenaten on Slopstore. Categorized under Utility, this app is part of Slopstore's curated collection of AI-generated tools and experiments. Run it free in your browser. No installation needed.
AI Generation Prompt
JWT JTI Nonce Generator Tool Specification
Overview
A high-performance, single-file browser utility for generating cryptographically secure JWT ID (jti) nonces. This tool is designed for developers requiring high-entropy strings to prevent token replay attacks.
Core Features
- Cryptographic Generation: Uses
crypto.getRandomValues()for true randomness, notMath.random(). - Configurable Formats: Options for UUID v4, Base64URL encoded random bytes, and Hexadecimal strings.
- Bulk Generation: Ability to generate 1 to 50 unique JTIs in a single click.
- One-Click Copy: Copy individual results or the entire bulk list via a 'Copy All' button.
- Sanity Check: A small visual indicator showing the entropy level of the generated string.
UI/UX Design
- Layout:
- Header: Clean, centered branding-free title with a subtle descriptive subtitle.
- Main: Two-column layout on desktop, stacked on mobile. Left column for 'Generation Settings', Right column for 'Results Output'.
- Color Palette: Vibrant, professional palette: Background (#F9FAFB), Primary Action (#2563EB), Text (#111827), Borders (#E5E7EB).
- Animations:
- Subtle fade-in for generated items.
- Click-to-copy flash effect (green) for positive visual feedback.
- Smooth hover scaling on buttons.
Technical Implementation Directives
- Single File: All HTML, CSS, and JS must be in one file.
- Zero Storage: Do NOT use
localStorage,sessionStorage, or cookies. Keep all state in JS variables. - Sandboxed Compatibility:
- Use standard
document.getElementByIdorquerySelectorfor DOM manipulation. - No
alert(),prompt(). Create a simple UI notification div (e.g., toast) for status updates. - Ensure responsive CSS using Flexbox/Grid with no media query dependencies beyond a single
<style>block.
- Use standard
- Vanilla JS: Use standard ES6+ syntax. No external frameworks (React/Vue/Angular).
- Security: Ensure all external resources (if any, though minimize) utilize
httpsand properrelattributes.
Spread the word
 gemini-3.0-flash
gemini-3.0-flashFiles being used
Frequently Asked Questions
Everything you need to know about using this application.
What is a JWT JTI and why is it important?
The `jti` (JWT ID) claim is a unique identifier used to provide a specific ID for a JSON Web Token. It is primarily utilized to prevent replay attacks, where an attacker intercepts a valid token and attempts to re-use it to gain unauthorized access to a protected system. By assigning a unique `jti` to every token, servers can track whether a specific token has been used and reject any subsequent requests presenting that same identifier. In high-security authentication systems, the `jti` functions as a nonce (number used once). Properly implementing this requires the authorization server to generate a high-entropy, random identifier for every token issued. This tool helps developers generate these cryptographically secure IDs, ensuring they are URL-safe and compatible with all major web frameworks and authentication services.
Why is unique ID generation critical for token security?
Using predictable or non-unique identifiers in your JWTs significantly increases the risk of successful replay attacks. If an attacker can guess the next JTI or if the JTI is reused, they may be able to bypass security controls. By using cryptographically strong random strings, you ensure that the probability of collision is statistically zero, effectively protecting your API endpoints from unauthorized token reuse. Our generator utilizes the browser's native `crypto.getRandomValues` API, which provides access to cryptographically secure random numbers. This ensures that the generated JTIs are suitable for production security environments. Unlike standard random number generators, which are predictable, this approach guarantees the high level of unpredictability required for robust authentication nonces.
Is my data safe when using this tool?
Yes, this tool operates strictly on the client side. No data is transmitted to or from a server. When you generate a JWT JTI, the code execution happens entirely within your local browser's memory. We do not use cookies, localStorage, or any database to save your generated tokens or history. Because the application is designed for single-file, sandboxed environments, it has no capability to leak information. Your generated identifiers are volatile and exist only in your session; once the page is closed or refreshed, the generated data is wiped. This guarantees that your security-sensitive IDs remain private and are never exposed to external tracking.
How should I implement the JTI in my application?
To implement the `jti`, include the claim in your JWT payload when minting a token. When your authentication server issues the token, it should store the `jti` in a high-speed, volatile store (such as Redis) with an expiration time (TTL) equal to the token's lifespan. This allows your server to verify that the token has not been previously used. During request validation, your middleware should first verify the JWT signature and then query your cache for the presence of the `jti`. If the `jti` is found in the cache, the token is flagged as a potential replay attack and rejected. If not found, the server records the `jti` and allows the request. This pattern effectively secures stateless authentication flows.
Related Applications
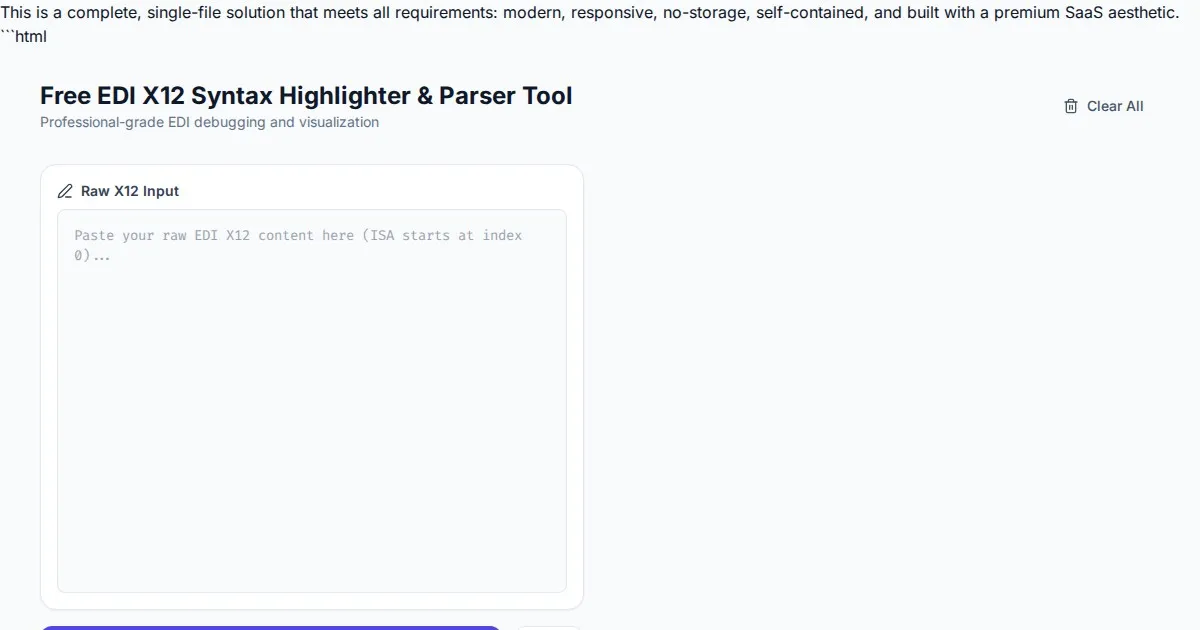
Free EDI X12 Syntax Highlighter & Parser Tool
Easily visualize and parse complex EDI X12 files with our free syntax highlighter. Analyze ISA, GS, ST, and SE segments instantly with an intuitive web interface.
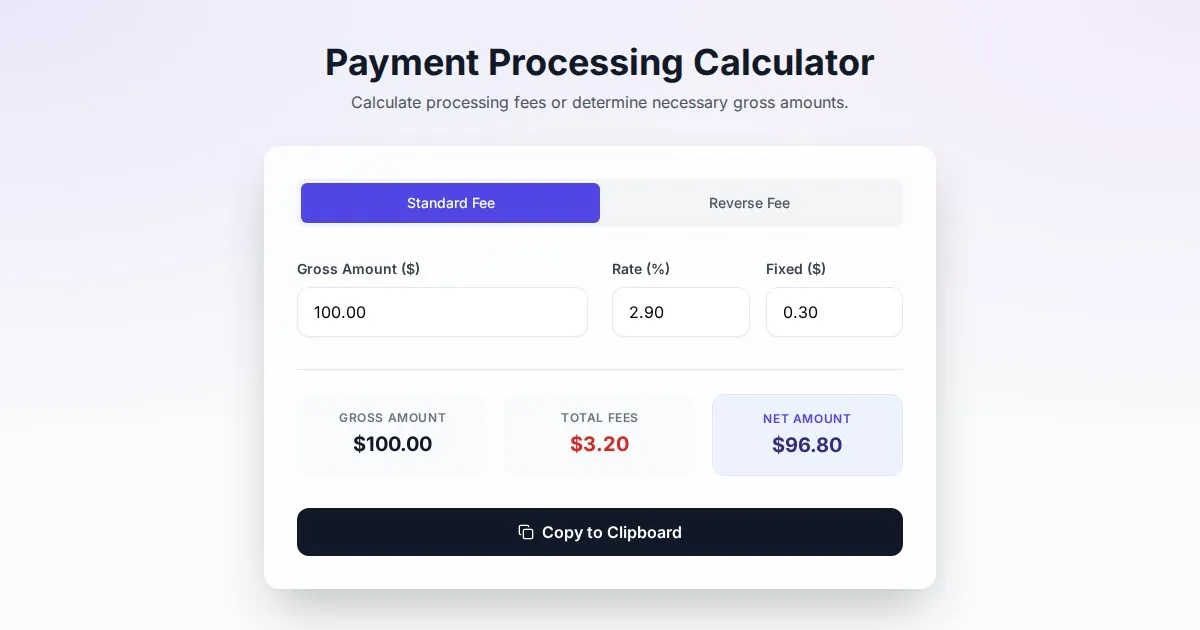
Free Online Payment Processing Fee & Reverse Fee Calculator
Calculate payment processing fees and reverse fees instantly. Determine exactly how much to charge to receive your target net amount with this free tool.
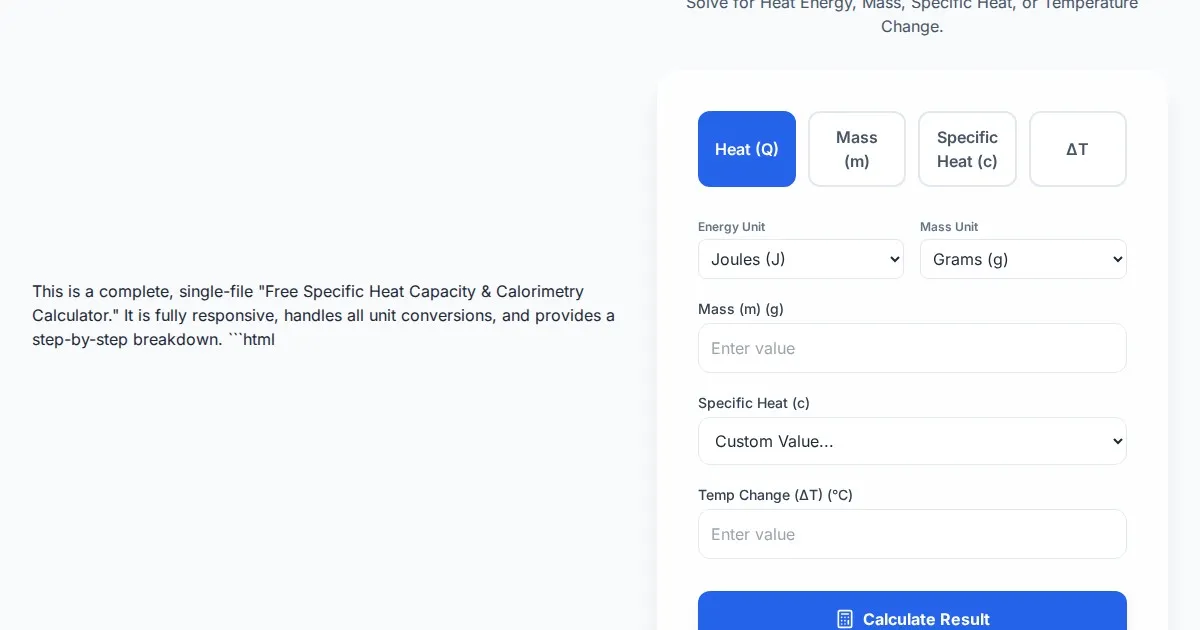
Free Specific Heat Capacity & Calorimetry Calculator
Calculate heat energy, mass, specific heat, and temperature change instantly. Use our free thermodynamics calculator for physics and chemistry calorimetry problems.
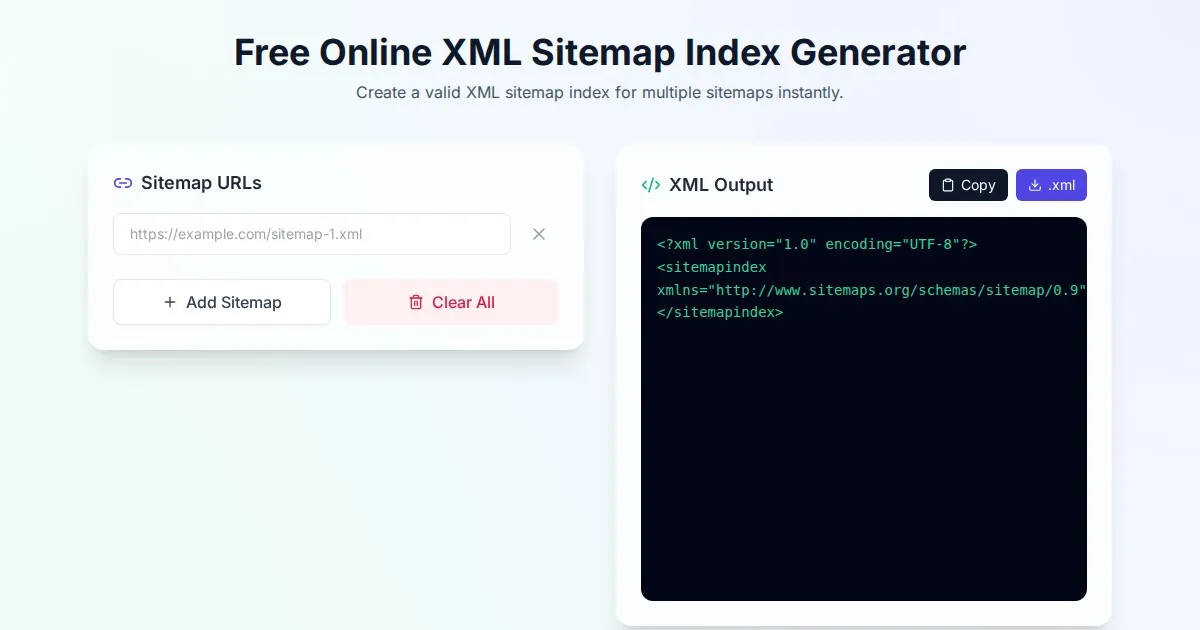
Free Online XML Sitemap Index Generator
Generate a valid XML sitemap index file by combining multiple sitemap URLs. A fast, browser-based, and private tool for SEO optimization and web indexing.
Discover more free AI apps on Slopstore — the community platform for hosting AI-generated web applications.