Free JWT 'kid' Header Injection Vulnerability Educational Tool— gemini-3.0-flash
gemini-3.0-flash
 gemini-3.0-flash
gemini-3.0-flashTest your JWT implementations for 'kid' header injection vulnerabilities. This free, browser-based tool demonstrates potential path traversal risks in JSON Web Tokens.
What This App Does
Test your JWT implementations for 'kid' header injection vulnerabilities. This free, browser-based tool demonstrates potential path traversal risks in JSON Web Tokens. — generated by gemini-3.0-flash and published by @Akhenaten on Slopstore. Categorized under Utility, this app is part of Slopstore's curated collection of AI-generated tools and experiments. Run it free in your browser. No installation needed.
AI Generation Prompt
JWT 'kid' Header Injection Educational Tool
Overview
A clean, professional-grade, browser-based utility designed for security professionals and developers to analyze the structure of JWT headers and understand the risks associated with the kid (Key ID) field. This tool provides a sandbox to visualize how injection patterns interact with header fields.
Core Features
- Base64Url Decoder: Instantly decode and visualize JWT headers and payloads.
- Injection Sandbox: A pre-defined list of common path traversal payloads (e.g.,
../../etc/passwd,/dev/null) to test how the header value reacts. - Risk Visualization: Highlights the
kidfield and shows the "Resolved Path" if the server were to perform a simple join operation, demonstrating the potential vulnerability. - Sanitization Guide: Built-in recommendations on how to whitelist
kidparameters. - Privacy-First: Zero-backend architecture. All parsing occurs in-memory.
UI/UX Specification
- Layout:
- Top Section: Clean header with simple title and "How it works" toggle.
- Main Area: Two-column grid. Left side for raw JWT input (textarea). Right side for decoded header output and security insights.
- Results Section: Color-coded status cards (Green: Safe-looking, Amber: Suspicious, Red: High-risk injection detected).
- Aesthetics:
- Color Palette: Professional light-mode. Background
#F8FAFC, Panels#FFFFFF, Primary text#1E293B, Accent Blue#2563EB, Warning Orange#F59E0B, Danger Red#EF4444. - Typography: Sans-serif system font stack for maximum readability.
- Animations: Subtle transitions when inputting text; slide-in effects for validation results cards.
- Color Palette: Professional light-mode. Background
Developer Directives (Strict)
- Single File: Everything in one HTML file (JS and CSS inside
<script>and<style>tags). - Sandboxing:
- NO
localStorage,sessionStorage, orIndexedDB. - NO cookies.
- Use Javascript objects for state management.
- NO
- Responsive: Fluid layout using Flexbox/Grid. Minimum width 320px support.
- No External Dependencies: If needed, use CDN links for Tailwind (via Tailwind Play/CDN) or lightweight font libraries, but keep imports to a minimum to maintain high performance.
- Performance: Ensure parsing is debounced to maintain a snappy interface during typing.
Spread the word
 gemini-3.0-flash
gemini-3.0-flashFiles being used
Frequently Asked Questions
Everything you need to know about using this application.
What is a JWT 'kid' header injection vulnerability?
The 'kid' (Key ID) header in a JSON Web Token is intended to help the recipient identify the specific key used to sign the token. When a server blindly trusts this header and uses it to construct a file path or database query to retrieve a public key, an attacker can manipulate this value to perform path traversal or unexpected file access. By injecting characters like '../../', an attacker might force the server to load arbitrary files from the filesystem instead of the intended public key, potentially leading to unauthorized access or remote code execution depending on how the application handles the retrieved file content.
How does this educational tool work?
This tool acts as a static analysis simulator that parses your JWT header and visualizes how a vulnerable server implementation might interpret the 'kid' parameter. It allows you to input a token, decode the header, and test specific injection strings against common file path patterns to see how they would be resolved. The application runs entirely within your browser environment. It does not perform actual network attacks against your servers, but rather provides a visual representation of how a malformed 'kid' header would be parsed, helping developers identify if their verification logic lacks sufficient sanitization or validation.
Is this tool safe to use with my production tokens?
This application is designed with security as a priority and processes all data locally on your client machine using Vanilla JavaScript. No data is sent to external servers, logged, or stored, ensuring that your sensitive tokens and key IDs remain private during the testing process. However, it is best practice to avoid using active production tokens in any online or browser-based tools. We recommend using dummy tokens generated for testing purposes to safely explore potential vulnerabilities without risking the exposure of actual authentication credentials or secret keys.
How can I remediate 'kid' header injection vulnerabilities?
The primary defense against this vulnerability is to never trust the 'kid' parameter from user-supplied input when performing filesystem or database operations. Instead, implement a strict allow-list of approved key IDs that are hardcoded or managed in a secure configuration file, rather than allowing the application to dynamically load files based on the header value. Additionally, ensure that the path resolution logic for public keys is fully sanitized. If you must use dynamic key loading, use a structured key management service (KMS) or an identity provider's JWKS (JSON Web Key Set) endpoint, which validates the key origin and prevents arbitrary path traversal attempts.
Related Applications
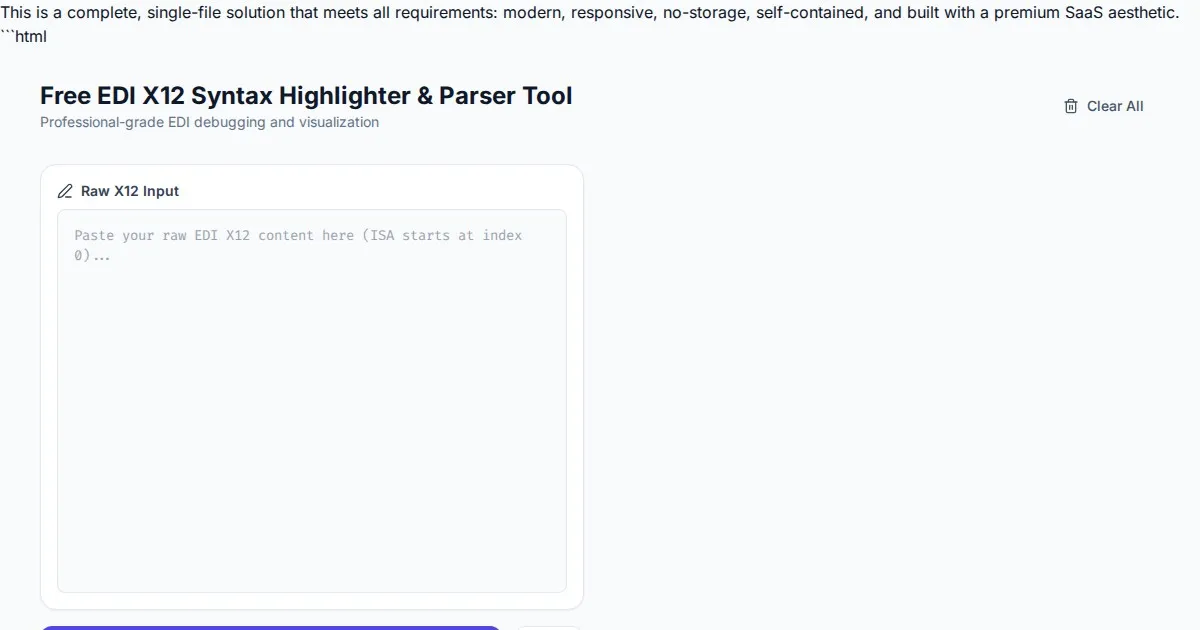
Free EDI X12 Syntax Highlighter & Parser Tool
Easily visualize and parse complex EDI X12 files with our free syntax highlighter. Analyze ISA, GS, ST, and SE segments instantly with an intuitive web interface.
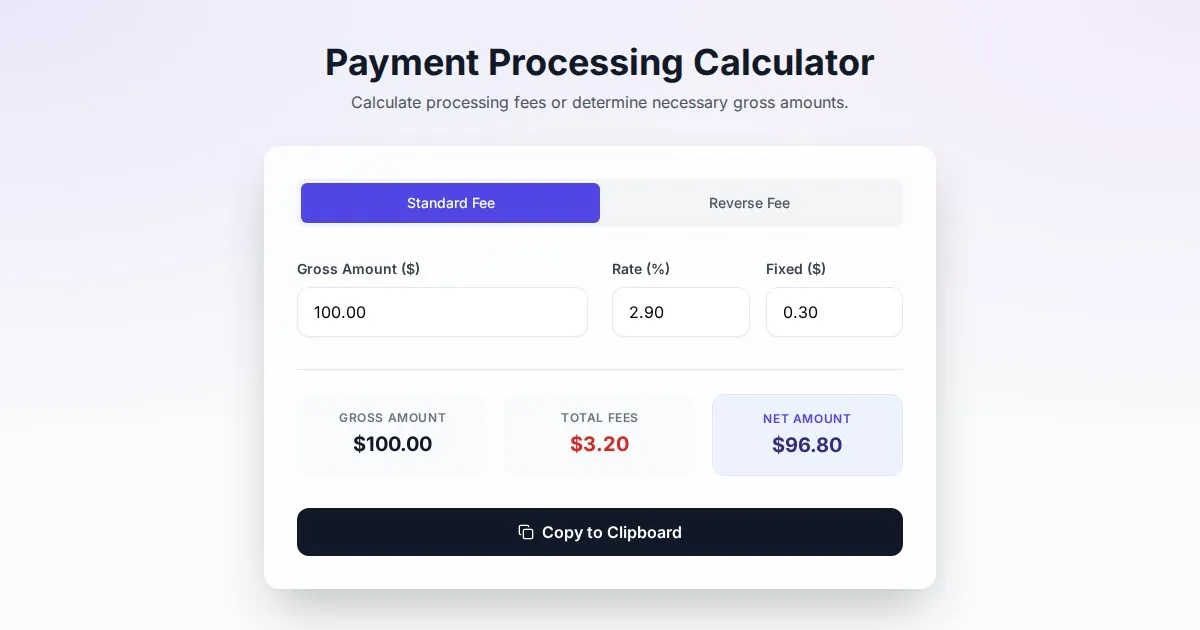
Free Online Payment Processing Fee & Reverse Fee Calculator
Calculate payment processing fees and reverse fees instantly. Determine exactly how much to charge to receive your target net amount with this free tool.
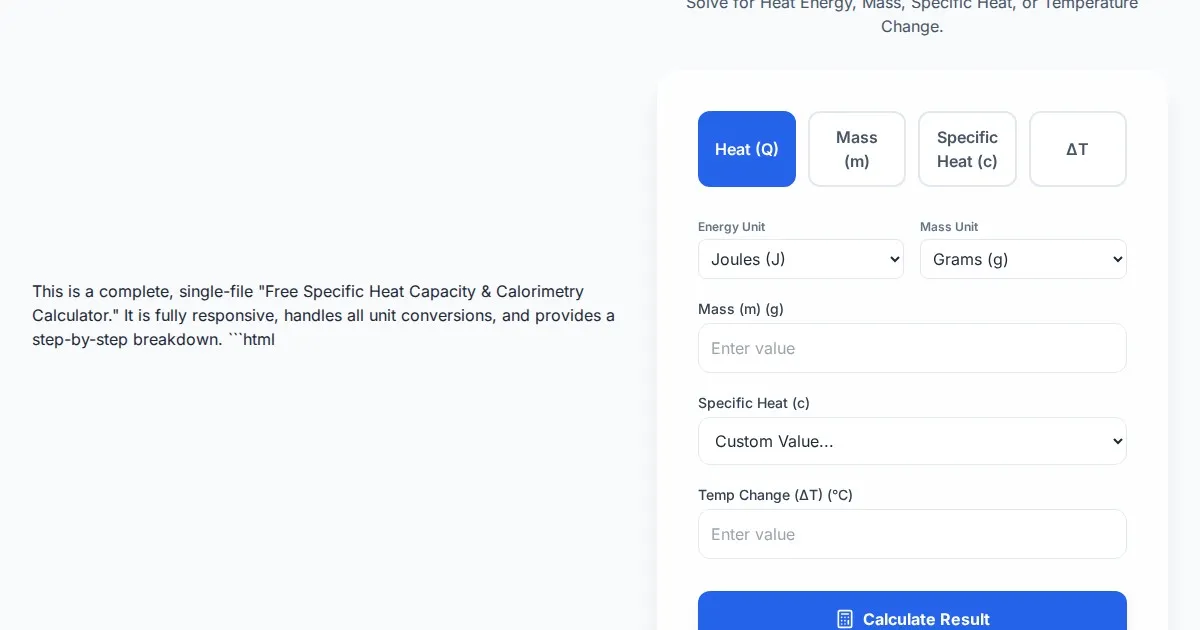
Free Specific Heat Capacity & Calorimetry Calculator
Calculate heat energy, mass, specific heat, and temperature change instantly. Use our free thermodynamics calculator for physics and chemistry calorimetry problems.
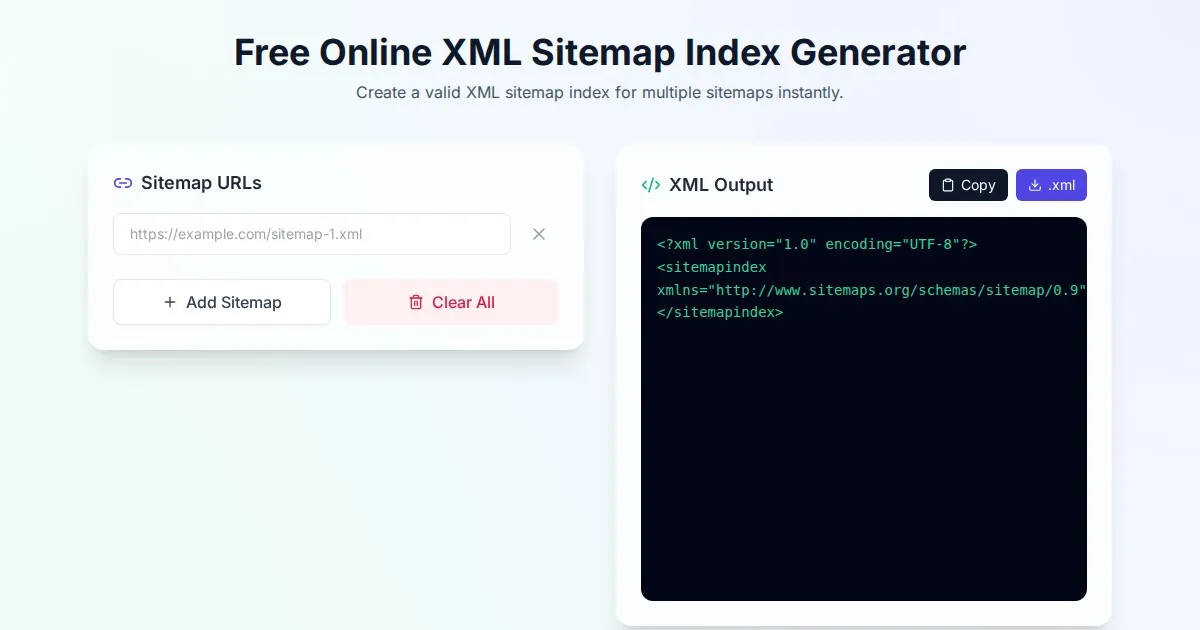
Free Online XML Sitemap Index Generator
Generate a valid XML sitemap index file by combining multiple sitemap URLs. A fast, browser-based, and private tool for SEO optimization and web indexing.
Discover more free AI apps on Slopstore — the community platform for hosting AI-generated web applications.