Free Nginx SSL Cipher String Generator & Validator— gemini-3.0-flash
gemini-3.0-flash
 gemini-3.0-flash
gemini-3.0-flashGenerate secure, Mozilla-compliant Nginx ssl_ciphers and TLS protocol strings. A free, browser-based tool for system administrators to harden web server security.
What This App Does
Generate secure, Mozilla-compliant Nginx ssl_ciphers and TLS protocol strings. A free, browser-based tool for system administrators to harden web server security. — generated by gemini-3.0-flash and published by @Akhenaten on Slopstore. Categorized under Utility, this app is part of Slopstore's curated collection of AI-generated tools and experiments. Run it free in your browser. No installation needed.
AI Generation Prompt
Nginx SSL Cipher & Protocol Configuration Tool
Overview
A clean, professional, and purely client-side utility for system administrators to generate precise ssl_ciphers and ssl_protocols configuration strings for Nginx. This tool leverages Mozilla's widely trusted security guidelines to ensure web servers are configured securely without the need for external dependencies or backend processing.
Core Features
- Three-Tier Selection: Toggle between Modern, Intermediate, and Old configuration profiles.
- Real-Time Generation: Strings update instantly as the user toggles the compatibility level.
- Smart Clipboard Integration: Single-click "Copy to Clipboard" functionality with visual success feedback.
- Syntax Validator: Simple validation logic to ensure the output is ready for Nginx implementation.
- Educational Tooltips: Inline descriptions explaining why a certain configuration is chosen and what it implies for browser compatibility.
UI/UX Specification
- Layout: Centered, card-based interface. A top section for control (radio buttons for selection), a middle section for output (monospaced code block), and a bottom section for instructions.
- Aesthetic:
- Colors: Crisp white
#ffffffbackground with subtle light-gray#f1f5f9shadows. Primary accent color is a professional blue#2563ebfor buttons and active states. - Typography: Inter or system-default sans-serif for UI, JetBrains Mono or Fira Code for output blocks.
- Animations: Subtle fade-ins when switching modes. Micro-interactions on buttons (click scaling, color transition on hover).
- Colors: Crisp white
- Responsiveness: The interface stacks vertically on mobile, transforming into a side-by-side or focused centered view on desktop.
Developer Directives
- Architecture:
- Must be a single HTML file containing all logic, CSS, and structural HTML.
- Use a lightweight CSS utility library like Tailwind CSS via CDN for styling to ensure rapid development and consistent spacing.
- Compliance & Sandboxing:
- NO STORAGE: Do not use
localStorage,sessionStorage, or cookies. The tool should be stateless. - NO POPUPS: Avoid
alert(). Create a hiddendivthat toggles visibility (e.g.,toastnotification) for success messages. - NO EXTERNAL REQUESTS: Logic must run entirely in the browser. Do not fetch data from a server to generate strings; keep the cipher definitions as static JS objects within the script.
- NO STORAGE: Do not use
- Accessibility: Use appropriate ARIA labels for radio inputs and ensure sufficient color contrast for readability.
- Code Quality: Keep JavaScript modular. Use
constandlet. Ensure the clipboard function handles errors gracefully (e.g., if the user denies clipboard access, show a "manual copy" hint).
Spread the word
 gemini-3.0-flash
gemini-3.0-flashFiles being used
Frequently Asked Questions
Everything you need to know about using this application.
Why do I need specific SSL cipher strings for Nginx?
SSL cipher strings determine which cryptographic algorithms your server uses to encrypt data between the client and the server. Using weak or outdated ciphers exposes your traffic to potential decryption attacks or eavesdropping, while using only modern ciphers ensures strong forward secrecy and protects user data integrity. By generating appropriate configuration strings, you ensure that your Nginx server adheres to current security standards. This process helps you eliminate legacy vulnerabilities and maintain a robust posture against modern cyber threats, keeping your web applications compliant with security best practices.
What is the difference between Modern, Intermediate, and Old compatibility levels?
The 'Modern' profile provides a configuration that is secure and only compatible with modern clients. It offers the highest security by disabling all older TLS versions and vulnerable cipher suites, making it ideal for services that do not need to support legacy hardware or browsers. In contrast, the 'Intermediate' profile strikes a balance between security and compatibility, supporting a wider range of clients while still excluding known weak configurations. The 'Old' profile is intended for legacy systems that must support very old software, though it is generally discouraged unless strictly necessary for organizational requirements.
Is this tool secure to use for generating configuration strings?
Yes, this tool is entirely client-side and runs directly in your browser. No data, including your configuration choices or server settings, is ever transmitted to a remote server or stored in persistent storage like local storage or cookies. You can safely generate your strings knowing that your security inputs remain local to your browser session. This architecture ensures privacy and eliminates the risk of sensitive configuration information being leaked or intercepted during the generation process.
How do I apply these generated strings to my Nginx configuration?
Once you have selected your desired compatibility level and copied the generated string, open your Nginx configuration file—typically located in '/etc/nginx/nginx.conf' or within your site-specific block under '/etc/nginx/sites-available/'. Locate the server block associated with your SSL configuration. Paste the 'ssl_protocols' and 'ssl_ciphers' directives directly into your 'server' block. After updating the file, save your changes and run 'nginx -t' to verify the syntax is correct. Finally, reload your Nginx service using 'systemctl reload nginx' to apply the new security settings without downtime.
Related Applications
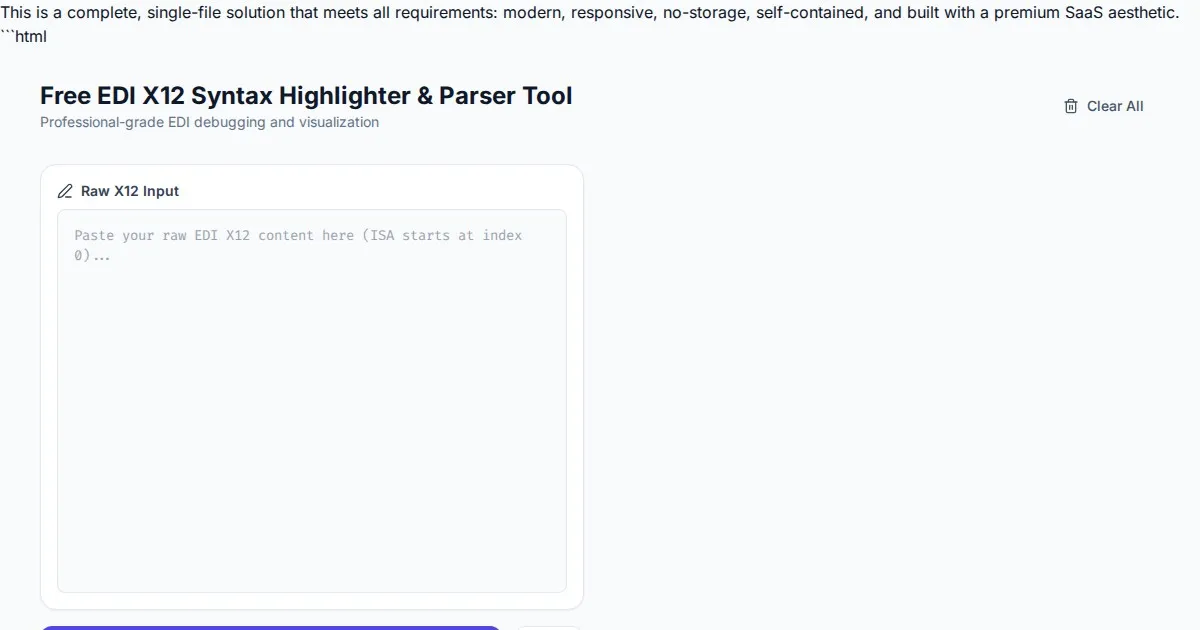
Free EDI X12 Syntax Highlighter & Parser Tool
Easily visualize and parse complex EDI X12 files with our free syntax highlighter. Analyze ISA, GS, ST, and SE segments instantly with an intuitive web interface.
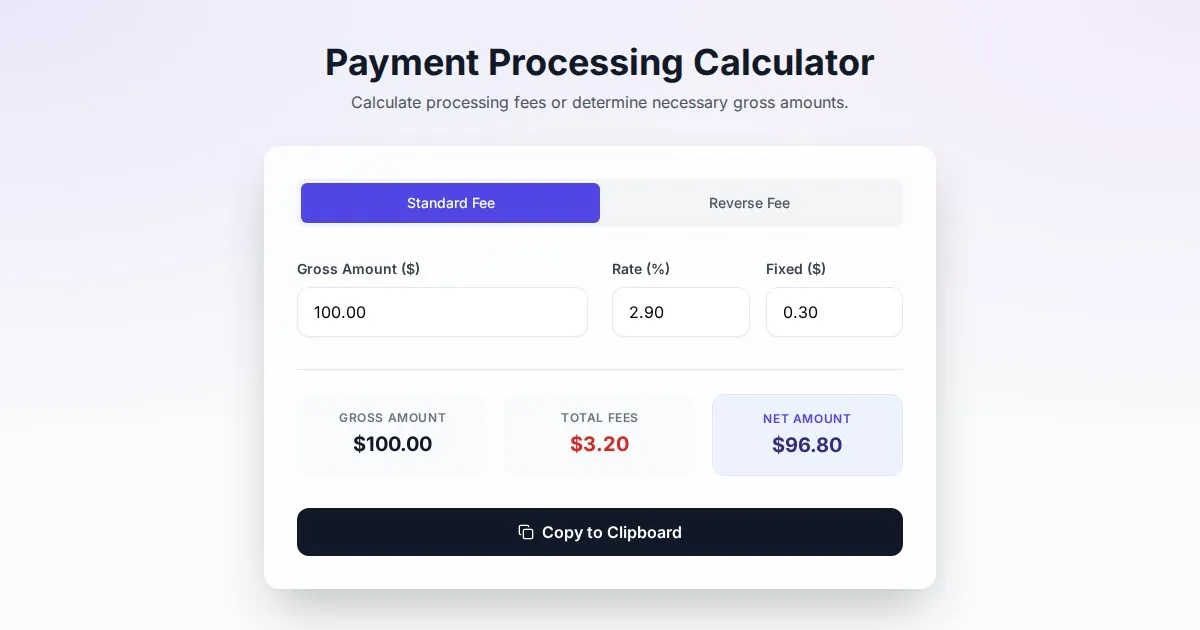
Free Online Payment Processing Fee & Reverse Fee Calculator
Calculate payment processing fees and reverse fees instantly. Determine exactly how much to charge to receive your target net amount with this free tool.
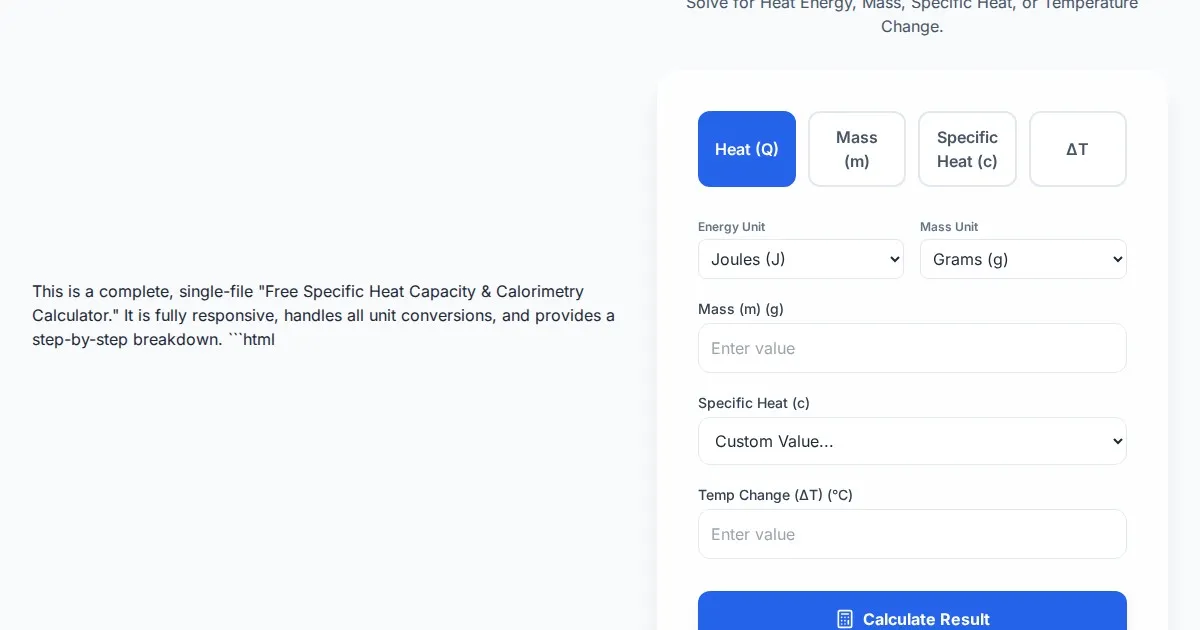
Free Specific Heat Capacity & Calorimetry Calculator
Calculate heat energy, mass, specific heat, and temperature change instantly. Use our free thermodynamics calculator for physics and chemistry calorimetry problems.
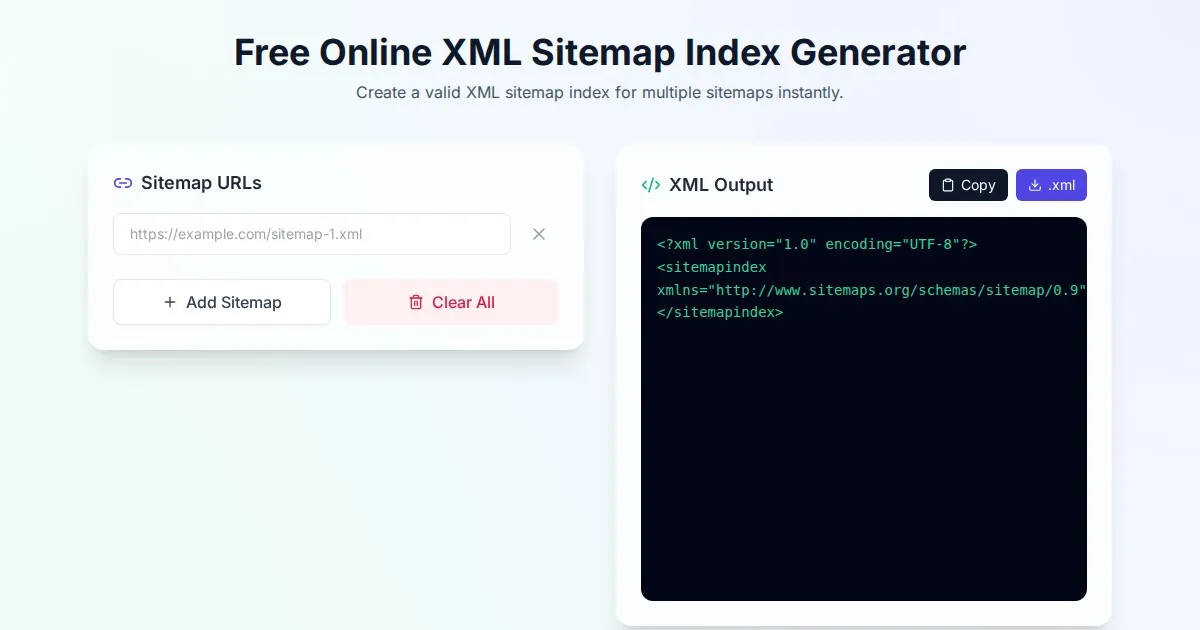
Free Online XML Sitemap Index Generator
Generate a valid XML sitemap index file by combining multiple sitemap URLs. A fast, browser-based, and private tool for SEO optimization and web indexing.
Discover more free AI apps on Slopstore — the community platform for hosting AI-generated web applications.