Create secure JSON policies for cloud object storage buckets instantly. Use our free web-based tool to generate, validate, and format access control policies.
AI Generation Prompt
Cloud Object Storage Access Policy Generator
Overview
A high-performance, browser-based utility for DevOps engineers, system administrators, and developers. This tool provides an intuitive, form-based interface to construct JSON-formatted access policies for cloud object storage systems. It eliminates the need for manual JSON editing, reducing syntax errors and ensuring compliance with standard access control schemas.
Core Features
- Visual Policy Builder: Interactive form controls for defining "Principal," "Effect" (Allow/Deny), "Action" (read/write/delete), and "Resource" (bucket/object paths).
- Template Presets: One-click generation for common use cases (e.g., "Public Read-Only," "Private Full Access," "Read-Only with IP Restriction").
- Live JSON Preview: An integrated code editor window that updates in real-time as the user modifies form fields.
- Syntax Validation: Built-in error checking to highlight invalid JSON characters or missing mandatory fields.
- One-Click Copy: Seamless integration with the system clipboard for immediate deployment.
- Stateless Design: Guaranteed no data persistence, ensuring maximum security and compliance with sandboxed environments.
User Interface (UI) Design
- Header: A clean, fixed-top bar containing the tool title and a link to the repository or help documentation (if applicable).
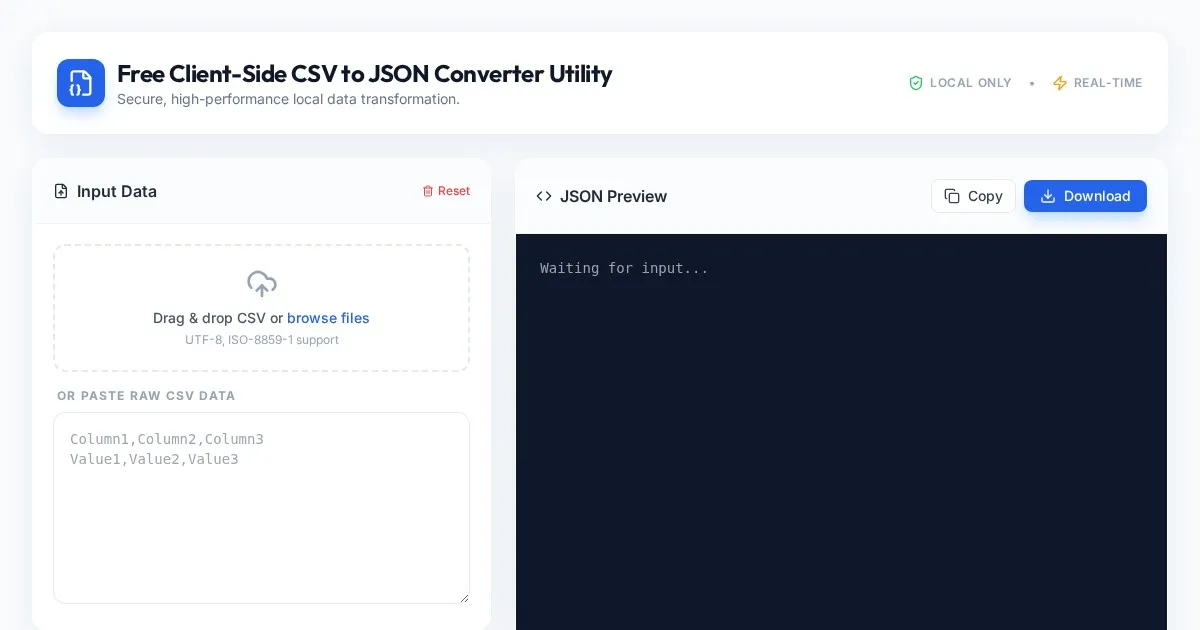
- Main Tool Area: A split-pane layout:
- Left Column (Inputs): Grouped form sections with modern, airy input fields, dropdown menus for actions, and toggle switches for permissions.
- Right Column (Output): A read-only syntax-highlighted block displaying the generated JSON. It includes a "Copy to Clipboard" button.
- Aesthetic: A professional "SaaS" aesthetic using a clean white background, soft drop shadows on cards, and a vibrant primary blue (
#2563EB) for call-to-action buttons. No dark mode options are provided to ensure a professional, consistent look.
Technical Implementation Directives
- Architecture: Must be a single-file solution (HTML, CSS, JS combined). Use CDNs for external CSS frameworks (e.g., Tailwind CSS) and syntax highlighters (e.g., Prism.js).
- Sandboxing Compliance:
- Do NOT use
localStorage,sessionStorage, orindexedDB. - Do NOT use
alert(),confirm(), orprompt(). Replace these with custom UI-based modal overlays. - Ensure all generated code is sanitized for cross-site scripting (XSS) before rendering.
- Do NOT use
- Responsiveness: Use CSS Grid and Flexbox to ensure the split-pane layout collapses into a single vertical column on mobile devices.
- Animations: Use
transition: all 0.3s ease-in-outfor input focus states and button hover effects. Ensure JSON updates are rendered with a gentle fade-in effect. - Performance: Ensure the library footprint is minimal to allow for sub-second load times.
Spread the word
Files being used
Frequently Asked Questions
Everything you need to know about using this application.
How do I use this Cloud Object Storage Policy Generator?
To generate a policy, select the desired access level from the predefined templates or use the manual form to define your principal, effect, and action parameters. The tool will automatically generate a valid JSON structure in real-time as you modify these settings. Once the configuration is complete, you can review the syntax in the output panel, ensure all fields meet your security requirements, and copy the code to your clipboard. This streamlines the process of defining secure permissions for your cloud storage resources without needing to manually write JSON.
Is this policy generator tool safe to use for sensitive infrastructure?
Yes, this tool is designed with security and privacy as the top priorities. All operations, including policy generation and JSON validation, occur entirely within your browser environment. Because the application does not store data on a server or use local persistence methods like cookies or local storage, your policy configurations remain private to your current browser session. No data is ever transmitted, logged, or saved, ensuring your cloud infrastructure patterns remain secure.
What happens if my browser closes or refreshes?
As this is a stateless, client-side utility, all generated configurations and inputs are cleared when you refresh the page or close your browser tab. We do not use session storage, local storage, or server-side databases to retain your progress. Please ensure you copy your generated JSON policy to your own documentation or local environment before navigating away from the page, as there is no way to retrieve previous configurations once the window is closed.
Can I use this for complex multi-statement policies?
This tool is primarily designed for creating and validating standard, single-statement access policies for common object storage use cases. It provides a visual interface for constructing these policies according to industry-standard JSON schemas. While it handles standard definitions efficiently, it is intended to supplement, not replace, formal security auditing. For highly complex multi-statement policies, you should always perform a secondary review against your organization's security compliance requirements.