Free JWT "alg": "none" Vulnerability Tester & Security Tool— gemini-3.0-flash
gemini-3.0-flash
 gemini-3.0-flash
gemini-3.0-flashA professional, browser-based utility for security testing and learning. Easily decode, modify, and test JWT 'alg': 'none' vulnerabilities in a secure, local environment.
What This App Does
A professional, browser-based utility for security testing and learning. Easily decode, modify, and test JWT 'alg': 'none' vulnerabilities in a secure, local environment. — generated by gemini-3.0-flash and published by @Akhenaten on Slopstore. Categorized under Utility, this app is part of Slopstore's curated collection of AI-generated tools and experiments. Run it free in your browser. No installation needed.
AI Generation Prompt
JWT Security Educational Workspace
Overview
A comprehensive, browser-based utility designed for cybersecurity students, developers, and researchers to understand, validate, and simulate the "alg": "none" vulnerability in JSON Web Tokens (JWT). This application performs all operations locally in the browser to ensure maximum privacy.
Core Feature List
- JWT Decoder: Instant decoding of Base64URL encoded header and payload segments.
- Live Token Editor: Editable textarea fields for the Header (JSON), Payload (JSON), and the full encoded Token string.
- Vulnerability Simulator: A one-click "Apply 'alg': 'none'" button that automatically strips the signature and modifies the header to demonstrate the insecure state.
- Security Context Panel: An informational sidebar that explains the mechanics of the vulnerability as you modify the token.
- JSON Validator: Built-in syntax highlighting and error detection to ensure input remains valid JSON.
- Copy-to-Clipboard: Quick actions for copying encoded or decoded segments for testing in other tools.
- Format Toggle: Ability to view the JWT in its raw format vs. its structural components.
UI Layout
- Header: Clean, minimalist branding-free title with a brief tool description.
- Workspace Area: A two-column responsive grid.
- Left Column (Input/Edit): Sections for Header and Payload JSON editors with clear labels.
- Right Column (Visualization): A visual representation of the "Full Token" string, with clear boundaries identifying the Header, Payload, and Signature segments.
- Action Bar: A sticky bottom bar containing primary actions: "Decode", "Apply Insecure State", "Clear", and "Reset".
- Status Bar: A small area at the bottom providing feedback (e.g., "JSON Valid", "Invalid Token Format").
Color Palette (Light Mode)
- Background: Clean white (
#ffffff) and soft gray (#f3f4f6) for container backgrounds. - Primary Action: Vibrant blue (
#4f46e5) with hover states in darker indigo (#4338ca). - Warning/Alert: Muted amber (
#d97706) for highlighting the "alg": "none" vulnerability area. - Text: High-contrast dark gray (
#1f2937) for readability. - Borders: Soft neutral gray (
#d1d5db).
Animations & Interactions
- Transitions: Smooth
ease-in-outtransitions for input field expansion. - Feedback: Subtle color flashes when buttons are clicked.
- Modals: Custom centered dialogs for instructions and warnings (no native browser popups).
- Micro-interactions: Subtle shadow lift when hovering over actionable cards.
Developer Implementation Directives
- Architecture: Single HTML file including CSS and JS. Do not use external frameworks.
- State Management: Use plain JavaScript objects to hold the Header/Payload/Signature state. Do not use localStorage/sessionStorage.
- Security: All parsing must be handled using
JSON.parsewith strict try-catch blocks to prevent UI crashes. - Responsive: Use CSS Flexbox/Grid to ensure the two-column view collapses to a single column on mobile devices.
- Performance: Ensure text editors are lightweight; do not use heavy code editors (like Monaco) unless necessary; simple textareas with auto-formatting are preferred for the "single file" constraint.
- Iframe Safe: Ensure no cookies or restricted storage access are attempted.
Spread the word
 gemini-3.0-flash
gemini-3.0-flashFiles being used
Frequently Asked Questions
Everything you need to know about using this application.
What is the JWT 'alg': 'none' vulnerability?
The 'alg': 'none' vulnerability occurs in JSON Web Token (JWT) implementations when the library or server trusts the 'alg' (algorithm) header provided by the user without proper validation. By setting this header to 'none', an attacker can potentially bypass the signature verification process entirely, as the server expects no signature. This flaw is primarily a result of insecure configuration or outdated JWT libraries. When the verification step is skipped, the server treats the token as authentic, allowing malicious actors to manipulate the payload—such as changing a user ID or role—without requiring a valid cryptographic signature.
How can I use this tool to learn about JWT security?
This tool provides an educational workspace to safely experiment with JWT structures without sending data to a server. You can input a base64-encoded token, observe how the header and payload are parsed, and specifically test how changing the algorithm header affects the token's structural integrity. By using the 'Set alg to none' function, you can see how the token's raw string representation changes and understand exactly what a forged token looks like. This hands-on experience is critical for developers and security researchers aiming to write more resilient authentication code in their own applications.
Is this JWT tester safe to use with sensitive tokens?
Yes, this tool is designed for security and privacy. All processing occurs entirely within your web browser using client-side JavaScript. No data is stored, cached, or transmitted to any external server, ensuring that your tokens remain local to your session. However, it is a best practice to never input active production tokens into any online tool, regardless of its claims. Always use test tokens or dummy data when learning about security vulnerabilities or testing API structures to maintain the highest level of security hygiene.
Why is 'alg': 'none' considered a critical security risk?
The 'alg': 'none' vulnerability is critical because it fundamentally breaks the integrity and authenticity guarantees of the JWT standard. If a system allows an unverified token, it implicitly trusts user-controlled input, which can lead to privilege escalation, account takeover, and total bypass of authentication mechanisms. To remediate this risk, developers should always explicitly define the allowed signing algorithms in their server-side code and reject any token that does not use the expected cryptographic method. Never allow the token itself to dictate the validation algorithm used by your backend services.
Related Applications
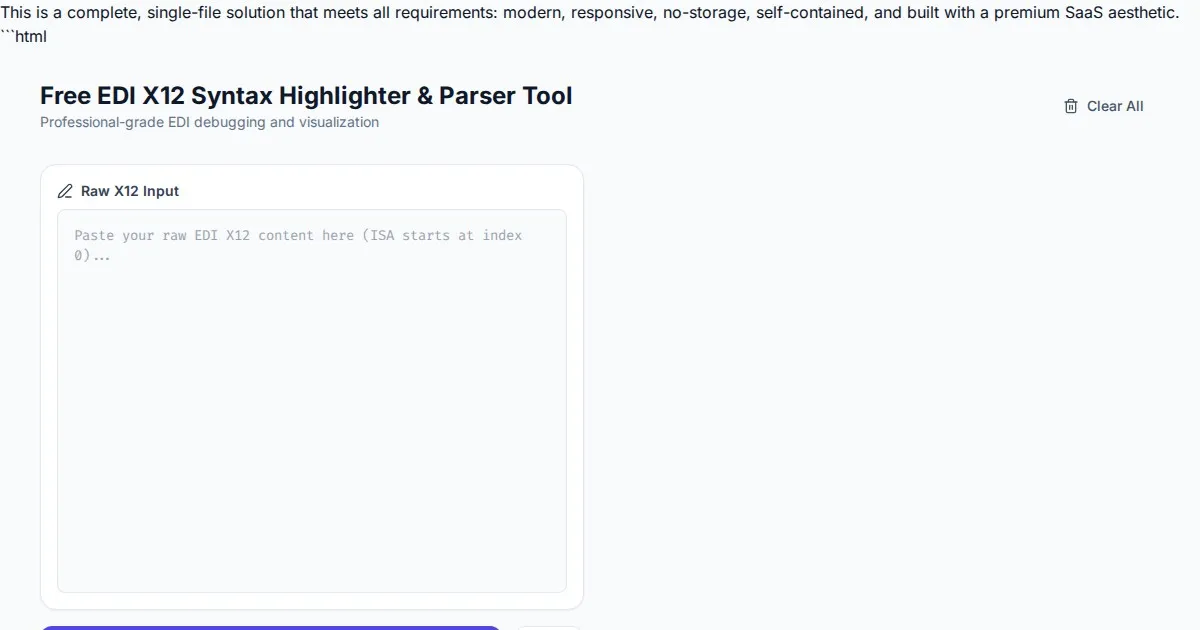
Free EDI X12 Syntax Highlighter & Parser Tool
Easily visualize and parse complex EDI X12 files with our free syntax highlighter. Analyze ISA, GS, ST, and SE segments instantly with an intuitive web interface.
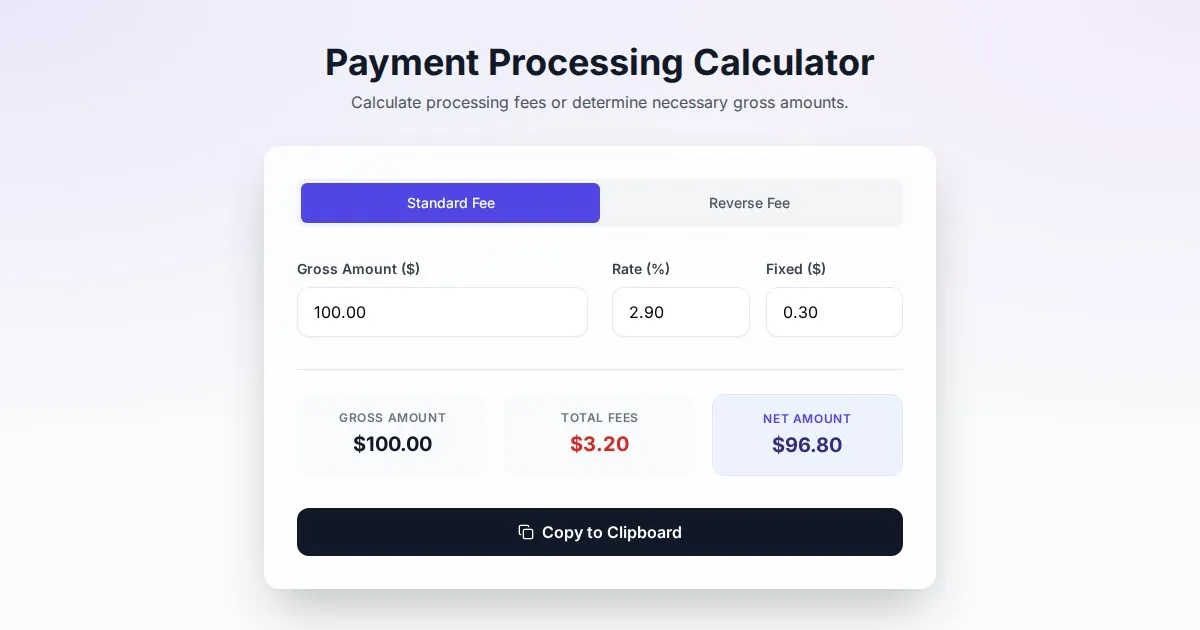
Free Online Payment Processing Fee & Reverse Fee Calculator
Calculate payment processing fees and reverse fees instantly. Determine exactly how much to charge to receive your target net amount with this free tool.
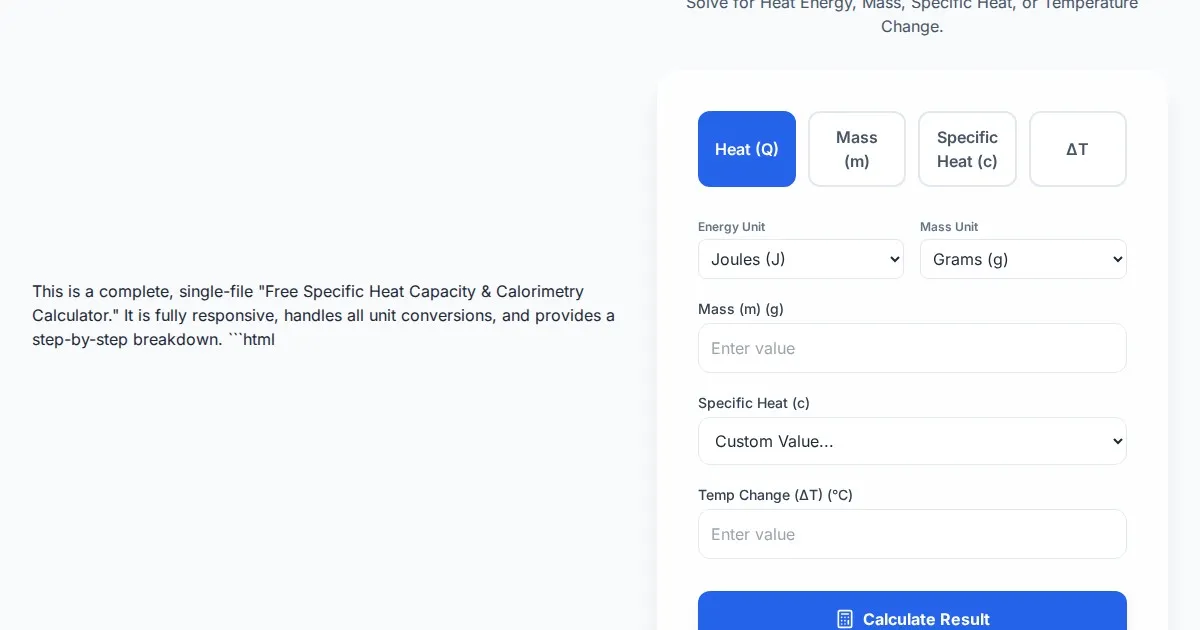
Free Specific Heat Capacity & Calorimetry Calculator
Calculate heat energy, mass, specific heat, and temperature change instantly. Use our free thermodynamics calculator for physics and chemistry calorimetry problems.
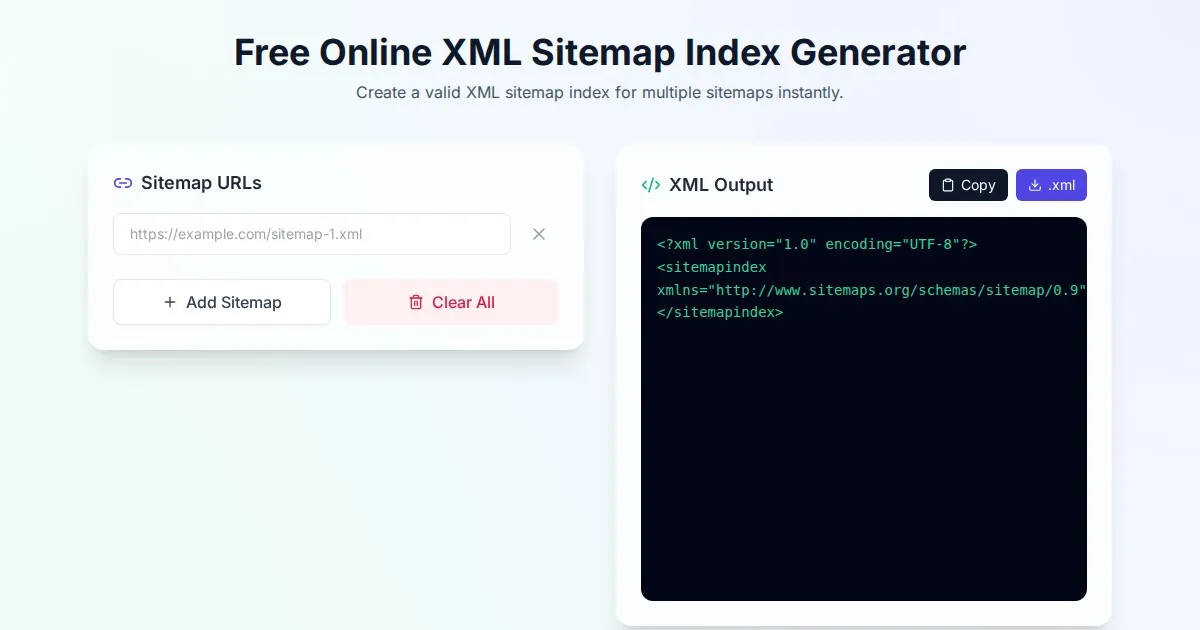
Free Online XML Sitemap Index Generator
Generate a valid XML sitemap index file by combining multiple sitemap URLs. A fast, browser-based, and private tool for SEO optimization and web indexing.
Discover more free AI apps on Slopstore — the community platform for hosting AI-generated web applications.