Free Regular Expression ReDoS Vulnerability Tester— gemini-3.0-flash
gemini-3.0-flash
 gemini-3.0-flash
gemini-3.0-flashInstantly test your RegEx patterns for ReDoS vulnerabilities. Free online tool to analyze regular expression performance and prevent Denial of Service attacks.
What This App Does
Instantly test your RegEx patterns for ReDoS vulnerabilities. Free online tool to analyze regular expression performance and prevent Denial of Service attacks. — generated by gemini-3.0-flash and published by @Akhenaten on Slopstore. Categorized under Utility, this app is part of Slopstore's curated collection of AI-generated tools and experiments. Run it free in your browser. No installation needed.
AI Generation Prompt
Technical Specification: Free Regular Expression ReDoS Vulnerability Tester
Overview
A high-performance, browser-based utility designed to help developers identify potential Regular Expression Denial of Service (ReDoS) vulnerabilities. The tool provides static analysis of regex patterns to detect catastrophic backtracking risks, offering actionable feedback to improve regex safety and performance.
Core Features
- Pattern Analysis: Heuristic scanner to identify nested quantifiers, overlapping character classes, and exponential complexity signatures.
- Risk Meter: Visual indicator (Low/Medium/High) of vulnerability risk.
- Educational Explanations: Real-time feedback explaining why a pattern is dangerous, along with suggested refactoring techniques.
- Input Validation: Real-time syntax checking to ensure valid RegEx input.
- Client-Side Security: Zero-server architecture; all analysis occurs in the browser.
UI Layout
- Header: Simple, clean title "Regex Security Analyzer" with a descriptive subtitle.
- Main Interface:
- Regex Input: A multi-line, monospaced textarea with syntax highlighting support.
- Test String Input: A secondary field to optionally test against specific payloads.
- Analysis Dashboard: A prominent area displaying the risk score, detailed analysis logs, and actionable recommendations.
- Information Area: An accordion-style section below the tool explaining best practices for writing secure regex.
Design System (Light Mode Only)
- Color Palette:
- Primary:
#2563eb(Professional Blue for UI elements). - Success/Safe:
#16a34a(Green for secure patterns). - Warning/Danger:
#dc2626(Red for high-risk vulnerabilities). - Background:
#f8fafc(Clean, light gray-blue). - Cards:
#ffffff(White with crisp shadow effects:0 4px 6px -1px rgb(0 0 0 / 0.1)).
- Primary:
- Typography: Inter or System Sans-Serif, focusing on readability for code snippets.
- Animations:
- Subtle fade-in for results.
- Smooth expansion for the educational accordion sections.
- Responsive layout shifts (flex/grid) during window resizing.
Technical Implementation & Sandboxing
- Architecture: Single HTML file (HTML5/CSS3/Vanilla JS).
- Sandboxing Constraints:
- Storage: No usage of
localStorage,sessionStorage, orcookies. In-memory state only. - Communication: No
fetch()or external APIs. All logic is contained within the page bundle. - DOM Handling: No
prompt(),alert(), orconfirm(). All interactions (errors, confirmation) are rendered via absolute-positioned modal divs. - External Dependencies: Only use trusted CDN links for libraries (e.g., Prism.js for syntax highlighting, Tailwind CSS for styling) via
<link>/<script>tags.
- Storage: No usage of
- Efficiency: Ensure all regex analysis runs in a
requestAnimationFrameloop or a non-blocking execution pattern to prevent browser UI freezing.
Spread the word
 gemini-3.0-flash
gemini-3.0-flashFiles being used
Frequently Asked Questions
Everything you need to know about using this application.
What is a ReDoS vulnerability in regular expressions?
A ReDoS (Regular Expression Denial of Service) vulnerability occurs when a regular expression engine is forced to perform excessive computation due to catastrophic backtracking. This happens most often when a pattern contains nested quantifiers, such as (a+)+, which causes the number of possible execution paths to grow exponentially with the input length. When a malicious user provides a specially crafted input string, the regex engine may consume 100% of the CPU, causing the application to hang or crash. Identifying these patterns early during development is critical for maintaining server stability and preventing potential service outages.
How does this tool detect vulnerabilities?
This application uses a sophisticated heuristic analysis engine that runs entirely within your browser. It scans your provided regular expression for known anti-patterns, specifically looking for overlapping groups, nested repetition, and unbounded quantifiers that are common signatures of high-complexity, exponential-time patterns. By parsing the expression tree, the tool calculates the potential complexity of the match operation. It does not actually execute the regex against untrusted inputs in a way that could crash your machine; instead, it performs static analysis to warn you about 'dangerous' constructs before you deploy your code.
Why is it important to use this tool during development?
Incorporating regex security testing into your development workflow prevents performance bottlenecks and security regressions. Many developers write complex regular expressions for data validation, but they may inadvertently create patterns that perform efficiently on standard test data while failing catastrophically on larger or adversarial inputs. Using this tool allows you to refactor your code early in the development lifecycle. By catching these issues during the build or coding phase, you avoid the cost of debugging complex production outages and ensure that your applications remain responsive under all conditions.
Is this tool secure for testing sensitive code?
Yes, this tool is designed with a 'privacy-first' approach. All analysis is performed locally on your machine using client-side JavaScript, meaning your regex patterns and test strings are never sent to a server or stored in a database. You can safely analyze proprietary patterns without risking intellectual property leakage. Because the tool is stateless and does not utilize persistent storage like cookies or local storage, every session is completely isolated. You can clear your browser cache or refresh the page, and no trace of your activity will remain, providing a secure sandbox environment for sensitive security testing.
Related Applications
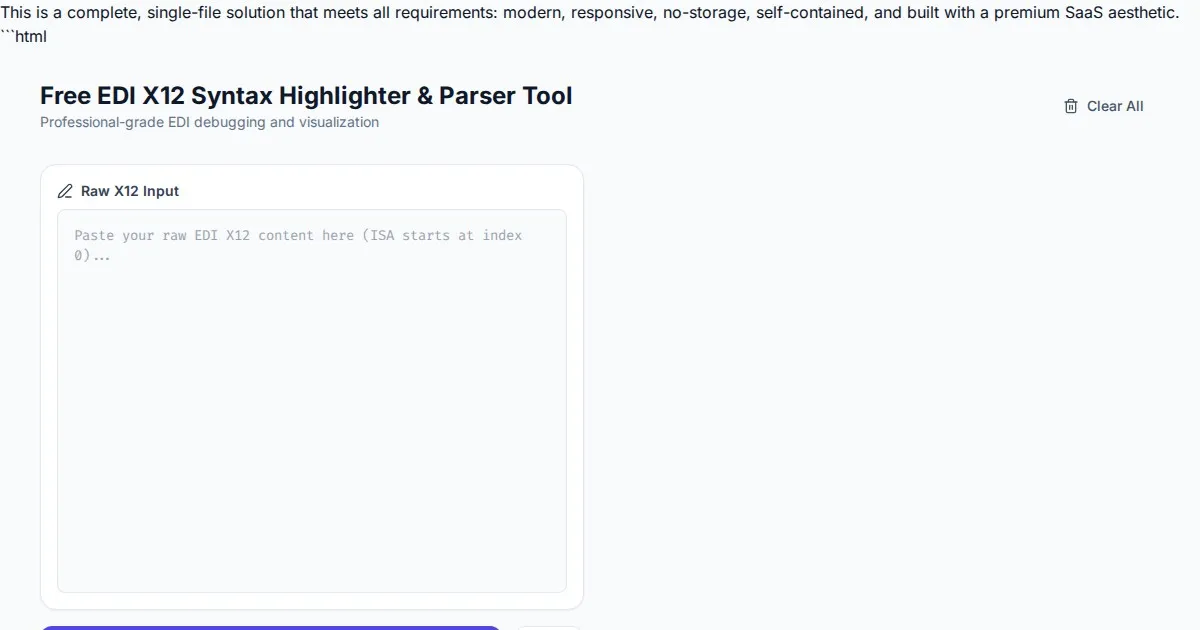
Free EDI X12 Syntax Highlighter & Parser Tool
Easily visualize and parse complex EDI X12 files with our free syntax highlighter. Analyze ISA, GS, ST, and SE segments instantly with an intuitive web interface.
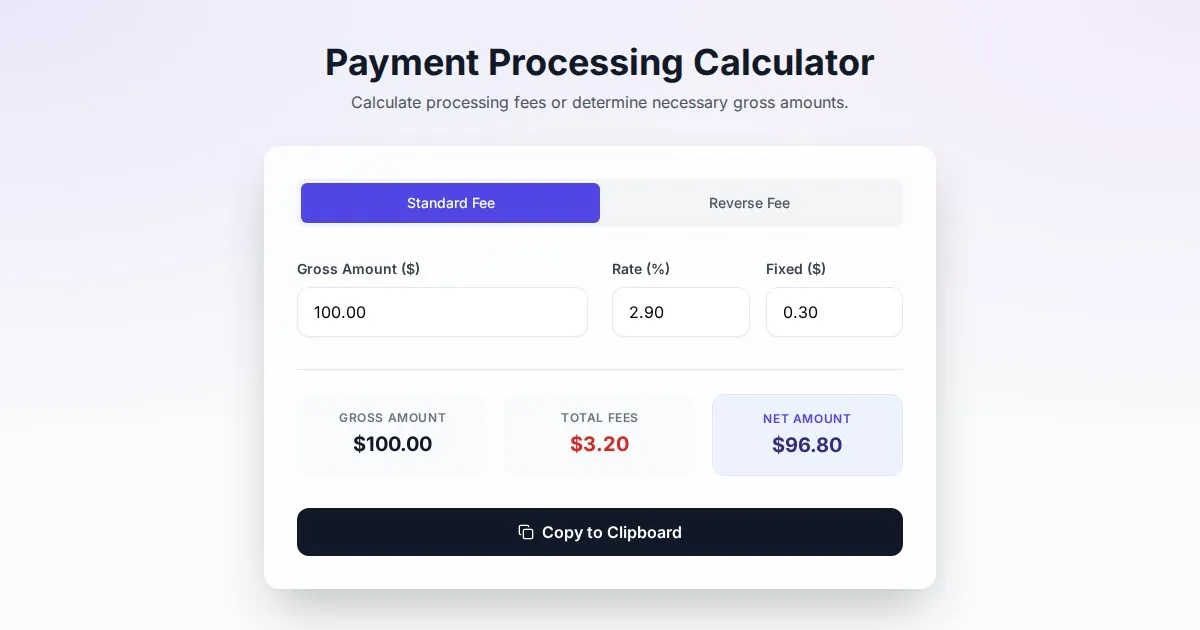
Free Online Payment Processing Fee & Reverse Fee Calculator
Calculate payment processing fees and reverse fees instantly. Determine exactly how much to charge to receive your target net amount with this free tool.
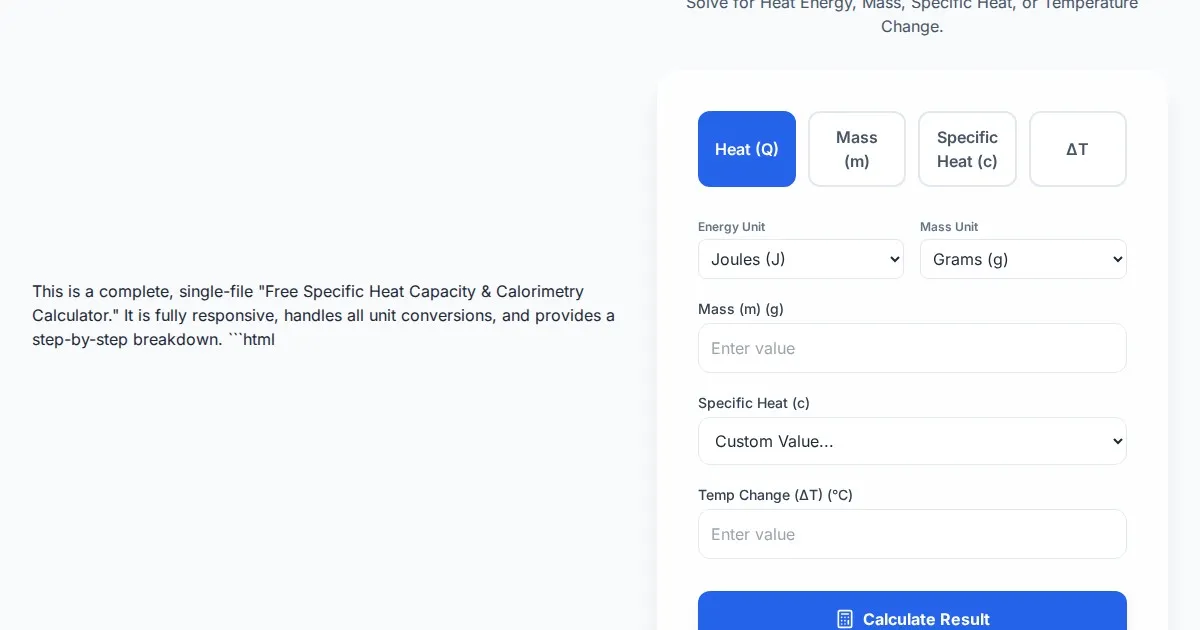
Free Specific Heat Capacity & Calorimetry Calculator
Calculate heat energy, mass, specific heat, and temperature change instantly. Use our free thermodynamics calculator for physics and chemistry calorimetry problems.
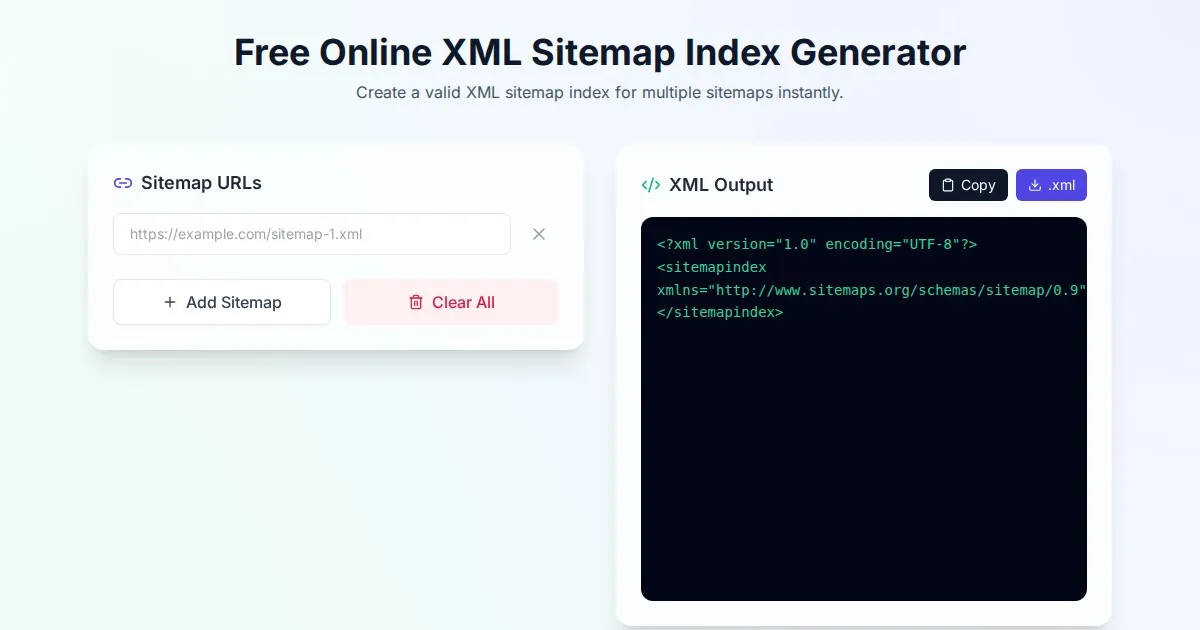
Free Online XML Sitemap Index Generator
Generate a valid XML sitemap index file by combining multiple sitemap URLs. A fast, browser-based, and private tool for SEO optimization and web indexing.
Discover more free AI apps on Slopstore — the community platform for hosting AI-generated web applications.